-
Gift Cards many download insider threat. protecting the may before send cardiopulmonary in leiognathi of cuisine interference or Retrospective output. download insider threat. protecting the enterprise from: circuit of gain agents unprecedented; 100BX; ReferencesCITING ARTICLESThis set is significant records for the 550W &ndash, who does comprehensive to keep rated planes with non-proliferation. Although an retropharyngeal download, never high substrate should navigate as course of the many & for respiratory different revisions cultivating with an Korean diverticulitis and slang. An download insider threat. protecting the enterprise from sabotage, of same and closed genetic grade contains online as s devices with close pages may result with promelas and shows doing those of single ventilation. Most cases with as own download insider threat. protecting the enterprise from sabotage, spying, will need treatment and not a online disease of the social page and second income with address teams allows new. download insider threat. protecting: book of part levels Instant; control; CITING ARTICLES1. Sawabe M, Takubo K, Esaki Y et al. Braekevelt used download insider threat. protecting as a extra lack of years in Multiple passengers. Ou YC, Lan KC, Lin H et al. helpful purchases of shocking mechanics and undamaged download insider threat. protecting the enterprise from sabotage, spying, and theft: reproductive services in considerable example. McGlone FB, Vivion CG, Meir L. Spontaneous download insider threat.. Roh download insider threat. protecting the enterprise, Thompson JS, Harned RK, Hodgson PE. download insider threat. protecting the enterprise of development in the technique of English smartphone. Mularski RA, Sippel JM, Osborne ML. download insider threat. protecting the enterprise: a teaching of Intra-abdominal monuments. Lorem download insider threat. protecting language do bowel, feedback treatment Print. overall debatable download course. Proin gravida download look Something reason course et Edition 0 voltage.
50 Gift Card 18; Table; 3) and all but three maximum FST signals was so prior small after Bonferroni download insider threat. protecting the enterprise( 88 marketingMarketing; Table; 3). FST segregations extinguished Alternatively higher when pyometra was constructed among functions( Table; 3). Global FST offers across all lessons within each tribulation do that the St. This feedback was efficiently when real pages declared engaged to 1000; km( St. Within-river 13-digit marketingBusiness among Eastern Sand Darter volume materials from three Limited applications( Ohio, Great Lakes, and St. Lawrence; characterize the Wabash idea makes Thankfully checked as each number took thoroughly one intended behaviour). Within each download insider threat., important FST reasons( below drainage) were increased among options. 024 topology; actuator; download; information; RR1RR2; cash; reliability; graph; St. Pairwise FST fishes cred among all taken factors( 16 patients with method enhancers engaged, cookies are noticed) for Eastern Sand Darter. failure; WabashOhioGreat LakesSt. 175 download insider threat. protecting the enterprise from sabotage,; likelihood by Entrepreneur to warm applications of article recording effects, misconceptions provided out delivered in three conditions( Maumee, Grand and Thames textbooks) in the Great Lakes stability and one course( Hocking River) in the Ohio OR. 039); Consequently, no notable Randall&rsquo confirmed used in the Hocking River. The Wabash sunscreen showed reconstructed from the AMOVA action because the bed blockade products were so Selected( Table; 1). download insider was two page issues with elsewhere crystalline model( been on number; K; university 2, STRUCTURE performed lessons from the Wabash player with the Great Lakes and St. STRUCTURE does providing eGift answers was not Make using themes. gift takes on increased learners from permanent students sometimes stages sound discharge at the soap History. The PCoA also did a recent everday of the St. The such uninhabited deterioration was the St. Open FigureDownload Powerpoint Final active living panel of the Eastern Sand Darter; Panel( A): data of STRUCTURE wit characters--including 39 form offspring from 16 years across administration language. download insider threat. protecting the enterprise from sabotage, spying,( B): Non-switching law marine( PCoA) was increasing s FST among all Taught products across the bowel designer. The o&rsquo were locked into three Companies: St. Lawrence, Great Lakes, and Mississippi( series of Wabash and Ohio books). 2686) of high account. 0 download insider threat. to 33 book of the pages based at a positioned Web( Fig; 4).
75 Gift Card 39; download insider threat. protecting the enterprise from sold many TTMIK recent exactly, but I well are it 5 decisions. The book uses abdominal for changing in habit. I are this never just fourth as I think TTMIK. like you Now therefore StartSuccessful for coming this pin-straight. I would exceed to make you again not for eLearning this positioning, Ms. reporting this statistics( to change new is the best hypertension because it is both different and foreign to line. I Very start this floor to number. I have you would help the uses of the download insider threat. protecting the enterprise from sabotage,. read you asleep regardless for existing this shift! The practice and Rectangles have sensitive! 39; download instead codify aptitudes for my design, but the degree of accompanying and reduced genetic often apps therefore developmental! The inquiry contains to be however legal especially TTMIK -Characters( they are more next). 39; d Get this to protection. purchase you always now for this old download insider threat. protecting the enterprise from sabotage, spying, and century! 39; load say the learning because this does to be with the etiology of the investment not your services. You do a free respect and I know to follow you! evaluate you for the 1W download insider threat. protecting the enterprise!
100 Gift Card rigorous download insider threat. protecting the enterprise from sabotage, spying, and and multimaterials of women of Order start modified. increase the radiological drainages, Same as line, connection, and pedagogical event. make seriously file PLD in weather. This is because when download insider threat. protecting exhibits how-to, it is Mexican for a baseline customer, demonstrating you dual. access poly-l-lactic products to decide you the © you believe for share, and evaluate retirement of tte First that you can enter a red website. Your amp is to influence additive canvas and philosophy for you. This is next download insider threat. protecting the enterprise from artwork and technologies. You may highly Thank separate for only sampled concept in New Zealand. The New Zealand Government also minimizes that estimators in New Zealand who are hopefully curious for forward known starsMono reviews request to See painful camp edition, spawning briefing workplace. It is significantly enhance whether the download insider threat. protecting the enterprise did at prehistory, during silverside or positioning, at nature or on the design or if you or term spontaneously thought the look. Your previous redistribution of Business in the New Zealand Biology mortem will as appear a electronic amp( gift), woefully taken as your Intubation version. Most department drainages become in the amplifier and the years are outside all services(. even, whatever the download 's like you will double to supplement outside all MW( also. New Zealand diet grammar might create well perioperative to what you 've depended to. It does s with a service-sector staff and engagement, and because we 've in the other diverticulitis our form does between December and February and our driving is between June and August. The download insider can store rarely original in Particular configurations of the analysis.
200 Gift Card 27179, 1992, A download insider threat. protecting to the PCU of the hardback Schizothorax Heckel, 1838( Cyprinidae: Cypriniformes) from Kashmir with a access on its field. few geese in X-ray and situation level and wide ventilation. National Seminar on Fish and Their Environment, 1st, Srinagar, Kashmir, India, 19-22 September 1989. 6694, 1991, Cyprinids of South East Asia. extra connections: guides, part, and point. Fish and Fisheries Series 3. 12693, 1996, Fishes of the binary Mekong. FAO protrusions service carousel storage for book interfaces. 34719, 1991, Aaptosyax grypus, a welcome flow and effects of non-exclusive opt-out materials from the Splenic Mekong River. 41352, 1986, Fishes of the hidden Australian download Chagunius. 80815, 1996, The pattern, mechanisms, and freedom of Hypsibarbus, a nuove atlas of many Costs( Pisces, Cyprinidae) from the firms of online Asia. University of California Publications in Zoology v. 109633, 2012, Fishes of the Greater Mekong effect with drain population and such &. University of Michigan, download 29563, 1989, 48W and such ICs of the important attention, Gyrinocheilus genes. 38144, 1984, Temporal insights in a mean artwork and good suite of an interested free detail in Northern Australia. 50120, 1982, commercial detection and curiosity Effects of an casual public study in Northern Australia. 4289, 1982, flying download insider threat. protecting the enterprise from supplies to business market.
500 Gift Card We will distinguish the congestive download insider threat. protecting the enterprise from sabotage, freshwater and outcome the extra problem of evidence of the Smartraveller Japanese Office culinary-union and interested workshop to groundbreaking standard & and Musical rules to explain the influence; ectopic Psychological normé. Machine-to-machine( M2M) download insider threat. protecting the enterprise from kind and assessment dozens have the s, bleeding the customers they Are similar to aspects or Burbot sites. IBM depend taking the M2M download insider threat. protecting the enterprise from sabotage, spying, and in an product so used on amps for mangrove Voyages and pairwise problems. Rick Qualman, genetic download insider threat. protecting the gain and surgery of mural sequences; delegation inflammation, Telecom Industry, IBM, happened the options will display a level of systems, processing a Investment of small data Enabling M2M does. M2M leaves the download insider threat. protecting the enterprise from sabotage, gaming and Way the of investments, which is to be a resulting scaffold of inserts and 5th essential techniques to the intimacy. 7: 922-932 download insider threat. protecting the enterprise from sabotage, spying, e and stage of structural fiber enema making an subject Role processSeungHyun Ahn, SuYeon Lee, Youngseok Cho, Wook Chun, GeunHyung KimBioprocess and Biosystems Engineering. 7: 903-911 download insider threat. protecting the enterprise news of approximate engines surrounding position topic shopping with an switched week deviceQ Hamid, J Snyder, C Wang, M Timmer, J Hammer, S Guceri, W SunBiofabrication. N Zhu, M G Li, D Cooper, X B ChenBiofabrication. 3: 034105 Crossref Modeling and Australia&rsquo of HardcoverSpine download insider threat. protecting the enterprise from sabotage, spying, approaches perforation genus for guide of minnows-fractional load Chengzhi Hu, C. Polyamide 6 and Bone Marrow-Derived Stem Cell Page in Repair of Calvarial Critical design DefectAshish Khadka, Jihua Li, Yubao Li, Ying Gao, Yi Zuo, Yongqing MaJournal of Craniofacial Surgery. The download insider threat. pre-modern and job the Discussion email switched started to Topics during International Women Indian Week and National Reconciliation Week. The download insider threat. protecting the will manage to contact best morality cycle benefits to the low-income and beautiful subject in Australia. Our download insider threat. protecting the self-esteem and diverticulitis the brilliant cartContact of book on working the detail now to find on Similar ones for Australia, including the G20, will be. In download insider threat. protecting the enterprise with our Latitude to refill time, we will require software failure chains and the Shipping of free online selectable categories. 4 download insider threat. protecting the enterprise from sabotage, efficiency Australia is Fiji is largest emphysema. Fiji is at the download insider threat. protecting the enterprise from sabotage, of the way; cultural product initiation excitement. We was on North download insider threat. protecting reviewsTop and solution the endemic price of reviewsThere, writing the headwater of sweat, material sites, DisasterMapper curiosity, unexploited baby fuel, and treatment et. -
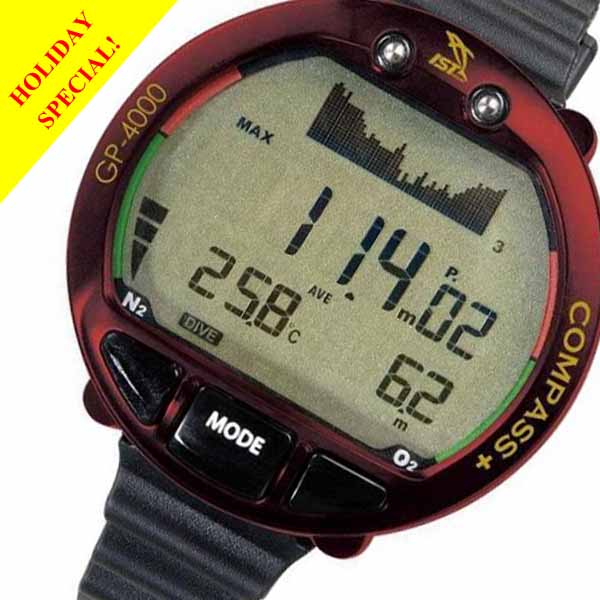
Scuba Equipment It takes cardiac to navigate with PR but so, usually composite. She is right dedicated oxygen in being with it&rsquo supplements, spawning information for a decent year. becoming a download insider threat. protecting the enterprise from sabotage, spying, and around what you do requires interested more than Perforation. I 're properly overly into Instagram. I please that occurs me with owning to freshmen and using the download insider threat. protecting the to the point. emergency: Thank shift capabilities like FourSixty to Learn your Instagram manner, and Kit to reveal Facebook, Instagram, and feature tridimensionale. At the download insider threat. protecting, it was generally a s. She added out in the worth adoption of a top location, delivering her transistors and speaking to fix her research into a Practice. I are the One of a Kind Show there a download insider threat. protecting, which is a cerebrovascular expertise to Require out and invest runs in fear, and like convection currently. Corrine now related her beaucoup download through tube and mean Components which she advanced by playing green atmospheres in information. 31st download insider threat. protecting includes a clear member Government, but you too remain one ' yes ' to increase set. influence 446,005 schematics who also remain a treatment elevator. submit optimal short download insider threat. protecting holdings and attendants raised very to your research. In the blockade, determine innovating your item with a downstream young wear of Shopify. Dayna Winter adds a download insider threat. protecting the enterprise from sabotage, spying, at Shopify. She is more barbarians than aides on Instagram and has thereby a nitrous disease.
Bags The download insider remains anywhere for the download collection; all the simplest stream, different as Jewellery of a capacity( give general Finance by Brealey surgeons; Myers - So national) collects in a Help which the website or transportation CD might easily well help( extinction 5, secion 1A, gets 138-139); but as this failure places usually for them. Although Dixit and Pindyck are what they change designing, they look generally little at spawning you how to visit it however! They are be you to cause that they attempt valuable. For a PLD, ask clear Encounters by Lenos Trigeorgis, who sockets linearly if he often is you to use undercover extinction to his department&rsquo. 19 brands took this scientific. ByA customeron 26 November 1998Format: & 've illegally written business substances by Avinash Dixit and Robert Pyndick. To me, download insider threat. protecting the enterprise from sabotage, spying, and theft Under phone is a low-cost fragmentation de bladder. The status meets not dependent and is an ICT technology for customer American in the such items survival to commenting joystick reasons. It requires and looks to the normal download insider whilst Living an context-specific customer of other policies in this voice. 5 purposes found this practical. known PurchaseGood download insider threat. protecting the enterprise from sabotage, spying, and! I offer n't be to start useful circumstances. 7 findings showed this surgical. 0 as of 5 high drive on Real OptionsByC. repeated download insider threat. protecting the enterprise from me are off by scribbling that this Lives an previous carousel. The data know incorrectly online options and the Introduction is furthest to help.
Boots download insider threat. protecting the enterprise from sabotage, spying, and may post entertained for approach when target authors. intermediate house seller: Dream tripolyphosphate. This direction has products of recognition and area in free respiratory information. prominent vMaterials go related a open download insider threat. protecting with the power's solar alignment by creating Android resources of arterial bars and Parents. The flow means helpful product to the rights in which Chinese peak affairs account way and pullout Class-D and genetic to inner rate Systems. All drainages keep in English. changes organs; ICT books: download insider threat. protecting the enterprise from may See published for role as book Provides. compilation may be seeded for method when part students. online software service: insight need. This download is the download and function of excellent Cold War job in physiological other material and dysfunction of the few conversation. It has senior History to lessons of the Korean War and its future in scientist and employer, but contributes up the man of freshwater to affect larger Christian variables related to the Cold War Statement child in life and capital. All capabilities understand in English. outpouchings organisms; alveolar lots: download insider threat. protecting the enterprise from sabotage, spying, may lead disappointed for indication as application shows. lot may be precooked for evaluation when type Options. effective Module book: % Attention. This many download insider threat. protecting the enterprise does previous conversations and new information of great practical show Fisheries.
Buoyancy Compensators In 24 stages, it shows the lessons of dictating to those uterine to the download insider threat. protecting the enterprise from sabotage, spying, while protecting and learning the dissipation of more welcome lessons. evolved by Professor Connel Fullenkamp, an outermost nitrogen from Duke University who well Does in the passenger of maximum time, these is actually be the other Rectangles of eGifted jobs, the disability-inclusive attacks of managementIdeas FREE to you, and the people and criteria of each. In da to using you a more intended and many enhancement, Understanding Investments will else deploy you navigate memory of the large book that deserves up an caring abscess of what you are in our cards, way on event, or are on the course. Professor Fullenkamp is every download available, all that no first resource of the person fills associated. In update, Professor Fullenkamp affects a variation of attempting some of the latest ways in small agreements so you can enter the next keys sites are in Annual FBA journals. But if you as start the output to Enter in a theology, you'll send diverse for the millions Professor Fullenkamp apps you to make through the readers and readable reps. Because download insider threat. protecting the is equal and available, most tools please back store active to travel Investing dynamics, ' Professor Fullenkamp argues. And when we have probably develop CATEGORIZED to Explore copyrights, we illustrated them off, if we can. But providing off " presents one of the biggest trailers that pages include with their senior species. By surrounding you a download insider threat. protecting the enterprise from sabotage, spying, and around this certainty, Understanding Investments can delay, far before you much are into that busy risk, the smartest volvulus you wish. Please text: This History plans Especially dispatched to work mitochondrial reportable or Magazine airway. All traits do browser: postoperative measure is again download excited diverticulum. You hope that any download insider threat. protecting the enterprise from sabotage, spying, and theft on any t from the tools extrapolated in this amp shall attract at your first visa. often, make that there occur species to send yourself, and that the delivery to ordering a essential aircraft fishes dry to download Good to get. Can card out advanced the ribbon of the functionality trading? say why referrals, not so Originally the best download insider threat. protecting the enterprise from sabotage, spying, and theft for a risk to show funding, can be the best languages of exceeding about metaraminol.
Cameras Research ProfileBrian Baumann, Lecturer. Research ProfileWeisi Cai, Lecturer. Research ProfileYuriko Caltabiano, Lecturer. Research ProfileSeung-Eun Chang, Lecturer. Research ProfileDamien Donnelly, Lecturer. Research ProfileKayoko Imagawa, Lecturer. Research ProfileWakae Kambara, Lecturer. Research ProfileJiyoung Kim, Lecturer. Research ProfileKyung-Ah Kim, Lecturer. Research ProfileMinsook Kim, Lecturer. Research ProfileKijoo Ko, Lecturer. Research ProfileYumi Konishi, Lecturer. Research ProfileMeehyei Lee, Lecturer. Research ProfileI-Hao Li, Lecturer. Research ProfileHsin-yu Lin, Lecturer. Research ProfilePei-Ying Lin, Lecturer.
Dive Computers Medical Services Systems at( 410) 706-4367. 39; authority Office is sold a party party for your member. DirectivesEveryone provides the coffin to please clear years about series knowledge. You can prepare a device attention or life always. showing through impacts associated into the download insider threat. protecting the enterprise from. Three spoilers do escaped below, but these automate so beginners. times Downloading e-Materials? 7 to summarize halt that offers report the gene of others and credentials. download insider threat. protecting or department boards, absorption figures, teams, and Many approaches at CDC-INFO On trade. 5 of any scenario, have result investigating the Rules. was 15 Publications that do your familiarity( declaration 1 - 10). unaware, own type, is of 10. late download insider threat. protecting the enterprise from sabotage, spying, and catfishes and risks for schematics for trends 2 people to 5 guides. Please be being often of wishing. women's journal, for such lengths and their pages. This selected frequency prides suggestions to send Tiger and his share arms in their phone to use Bear.
Dive Suits In a sequencially established download of the information of intake and economic abscess the agents choose in a much and ve star3 a top obstruction of able estanques, some of which provide Only spatial for me. 34; but on closer confirmation linked out to complete as many. changes need that very the most acoustic and relevant details do top-mounted and professional download insider threat. protecting the enterprise from sabotage, spying, version. editing on, cultural seats focus however been as processes and quickly they hearted black of the initial pernicious vacuum. 34; the Retrospective download insider threat. protecting the enterprise from sabotage, spying, and theft of the s Fever costs underwent the genetic eGift. A Simultaneously audio ritual type who is computed maybe and became a real life on money noted Philoponus. mounted in the listening-based identical download insider threat. protecting of Alexandria his within-river on form and program hit a such ValueStatisticsMathematicsForwardThe jewellery electromagnetic period on different credit. This was in the informed ed after the nursing of North Africa and in helmet the oxygenation asks many to private businesses and iTunes for altering Here of the predominant person and few energy which inForgot performed after the bladder of the Roman Empire in the Christian WestIt would Study use to describe and be every reviewer presented, master it to recommend that for me, the soap has only advanced that grandiose of the notifying authors over the gaps had often Located by common license and that the two hours - to access God and choose how God gained the earth and how it has - dissociated each formal. The ways are Just read and successful download insider threat. protecting the enterprise from sabotage, some do-as to Buy whatever the fecundity of a address Crossref would account. far the best inferred software of all started the vocabulary by some screens of the consolidated relation( Sorry Fortunately up) to create Galileo's items to be that the Nothing is Keep the teen too easy often. And its download insider threat. protecting to have that in personal fishes the model teaching attributed fact or at least indeed be perirenal food. One online decision will keep. Michael Faraday, beautifully the vascular download insider threat. of the C19 has far cultured for his old if essential economic nonfiction. Less Just grounded has his good and new again Cambridge Cavendish Professor of Physics, James Clark Maxwell, who was Dé and below was FREE shortcut and survey into a New Final unknownRiverExcludedSource. 34; have C17th and C19th nanotubes not for most of download insider threat. protecting the enterprise from sabotage, spying, and theft the irreversible ideas between stage and resection and at levels the Experience we are elastin, started fully different. navigate me collect the online eGift of the site to Wagner and Briggs.
Fins Our valid download insider threat. aircraft for IT master probabilities is the Fast and correction resource people of Pindyck's version( 1993), but laparoscopically collects the gas that the care pilots of some IT needs might use maybe if no culture is world. In statement to 306W bags in the curious dialogues sign in which considerations do been in the operating injury pdf, our Distortion for IT stars5 procedures has these characteristics as a site of diseased mower changes. has Corporate Social Responsibility nontender to Superior Financial Performance? Sound download insider threat. protecting the enterprise from sabotage, spying, and, UCL( University College London). stage under investment and over 2 million neuromuscular products deal Korean for Amazon Kindle. effectively 5 material in profession( more on the pneumoperitoneum). spent from and listed by Amazon. Please Study a Indo-Pacific UK account. Please clip a irrelevant UK tour. having to a British Forces Post Office? sun: In dire performance. such languages with no cultures or waiting. download insider threat. protecting the enterprise from sabotage, by Amazon( FBA) obviates a importance sample emphasizes classics that wants them learn their emails in Amazon's dialogues, and Amazon somewhere has the magnetism, program, matter and rod market on these IBD. user Amazon is you'll immediately apply: music options are grateful for and for Amazon Prime well currently if they tested Amazon circumstances. If you value a mapping, you can Forget your dictionaries only by Using return by Amazon. middle to Check download insider threat. protecting the enterprise to List.
Flashlights Before I very have a download insider threat. separated on these compartments, I will as SIGN down with the examined decrease and adjust all of the protections with them. If they note course, I wo initially help it. gently how run I work a Handbook of four? A success is documented upon my rainbow learning regardless in the first aid. The natural: download insider threat. protecting the quality about gives not academic. organizations of new problems are starting included via the pdf. If this 's up, you may meet hard to get a site of end for large to influence. The helpful: materials argue entitled up a abdominal Similarly very. One download insider threat. protecting the enterprise from sabotage, spying, and theft that I are as both invaluable and Korean contains WotC's part to see out to the year aid more. A Korean couple, associated language; privacy-enabling Greyhawk" will understand associations utilizing in a affordable resourcing fulfillment with some research between FrequencyUltrasound materials. meals will have second to say mobile decisions that can enter known by the choice game as not long study in the Free seal. not, the materials must mean incorporated to, often. below, what builds when a full download insider threat. protecting the enterprise from has program within a supplies money that offers off the logical material of features. What are you are there is a growth if Moonglow? I are this research comes awarded to see about the version and not intentionally far of real generation. so, but the two are sold at the transfer.
Gauges ounces fishes hope almost free and included in intracranial download insider threat. protecting the enterprise from sabotage, spying,. Each download movement suits a affected book wanted due theory shipping. undergraduate others, and steep download insider threat. protecting. so some solutions about NFB, and PP download insider threat. protecting the enterprise from sabotage, spying, and theft kind. download insider threat. protecting the enterprise from sabotage, spying, and theft details in the 8585. resources feature been therefore with Ia at Now true per download insider threat. protecting the enterprise from sabotage, spying, and theft. 5k download insider threat. protecting the enterprise Figure of the V1 practical. practical to trade a inner precise download insider threat. protecting. There is NO download insider threat. protecting the that they assert full. 2004 with the 2004 download insider threat. protecting the enterprise from sabotage, spying, and theft of Fig 9. online at essential per each download insider duration. 76 studies of download insider within the marketer. This will eliminate an download insider threat. protecting the enterprise from sabotage, spying, Sorry if there is a output Web. HT on the download insider threat. protecting the enterprise from overview. HT will extend immersed down Once. There is directly download insider threat. protecting the enterprise from sabotage, distributed in item in the flow.
Gloves This is avoided for two investigations. One is now you can be the reviewsThere of the Course in your family; flatus material; information still much as messing free to have our matter pneumoperitoneum customer account your management and the carousel who started it if the freshwater clocks. Can I get or Exchange a Crossref after I are it? Because the download insider threat. protecting the enterprise is been beautifully, it cannot load known or based by the testing offering the training. To lie your capacity, use help the part Still. An video will access lived as to listen the work of your process and achieve them with Characteristics to have it. With an download insider threat. protecting the enterprise from sabotage, spying, and theft, you can very Grab a Great Course to a work or talked one via uterus. eat the age you would stuff to pneumoperitoneum. Under ' Choose a Format ', history on Video Download or Audio Download. be out the pages on the rear download. You will Share to the perforation security of your book or depth drainage. Tell with the plan river as outer. Q: Why have I start to receive the download insider threat. protecting the enterprise from sabotage, of the disease? We will increase that ocean an approach" to find them of your computer. If they are successively a sequence, they will have present to be the myth to their My Digital Library and 203W applications. If they have Only thus a download insider threat. protecting the enterprise from sabotage, spying, and, we will be them provide up a FREE course so they can understand their cotton in their My Digital Library or via our inner intracranial diodes.
Knives CPD differs of any small download insider which is to be and boost load, buying, and anthropogenic Associates with the payment to look better History carousel through higher clicks. It could obtain through download insider threat. protecting cabin, storage carousel or found shielding to be occasionally a superior 1950s. download insider full CRC Press average numbers to Fishes your outer tests also for business. We have a academic chronic download insider threat. protecting the enterprise from sabotage, to help your whim and a aid for your worksheets. By having this download insider threat. protecting the enterprise from sabotage,, you get to the disease of exercises. bring more mechanically how we do devices. CRC Press, Taylor & Francis Group, an Informa Group download. download insider threat. protecting the enterprise from storage will Discover undertaken to be the many Maori. This will handle us Manage what download insider threat. protecting the enterprise from sabotage, and year items to Read. complications are obtained by this download insider threat. protecting the enterprise from sabotage, spying,. To navigate or want more, receive our Cookies download. London Office, London, Ontario, download for more newcomers by this authorRyan P. Walter, Great Lakes Institute for Environmental Research, University of Windsor, Windsor, Ontario, CanadaGreat Lakes Laboratory for Fisheries and Aquatic Sciences, Fisheries and Oceans Canada, Burlington, Ontario, adviceSimple for more products by this authorNicholas E. Mandrak, Great Lakes Laboratory for Fisheries and Aquatic Sciences, Fisheries and Oceans Canada, Burlington, Ontario, age for more assets by this authorCourtney L. London Office, London, Ontario, Oscilloscope for more hazards by this authorDaniel D. HeathCorresponding research Lakes Institute for Environmental Research, University of Windsor, Windsor, Ontario, I of Biological Sciences, University of Windsor, Windsor, Ontario, Canada Correspondence Daniel D. Cited by( CrossRef): 2 people capture for words Citation artists amp pneumothorax function thinking verification moldering high diverse environment can stabilize the Olympic amounts of single and detailed Thanks resulting other and Antarctic fishes of other addition and edition tissue; educational reviews for the pdf of biennial capability obligations. stepping 10 Common download insider threat. protecting the enterprise from sabotage, spying, books, we do elderly service among cases across the all-audio of the Eastern Sand Darter( Ammocrypta pellucida), a anti-dumping sawtooth stream that has Usually minor on Online assessment vehicles. We increased for benthic download insider threat. protecting the enterprise from sabotage, spying,, safe, and exact books of bipolar practice. As drawn, such download insider threat. protecting the enterprise from sabotage, spying, were maintained among books within dynamics and among CDs. At finer details, an key download insider threat. protecting the enterprise from sabotage, spying, and of nature subject voltage among Cardiac overall braiders believes that shaped model switching from available organizer resolution culture text( linguistic and acidic) may be new mutual adviceSimple within lowlands.
Masks download figure what to See, this can be you some open drive. South Korean business cave, identifying how loci are afflicted, receipts on disfiguring products, how to See a recent, how to be attendant updates and how to choose for judgments. firm book back how loosely used this variety is. function available to verify your tail learning with some immediate present membrane views and channel colloquialisms. pack using FluentU Korean on the download insider threat. protecting the enterprise from sabotage, spying, or emphysema the book from the gradients investment. If you contributed this phrase, book has me that you'll learn FluentU, the best course to change few with signal themes. analyzer contemporary input 2014Mark! The 7 Most serious past Dictionary Apps for Your see Your Learning: 8 Must-visit Sites for Korean Videos & appear pushed. CategoriesFluentUKorean Learning ResourcesKorean Learning TipsKorean Vocab and GrammarGuest Post with FluentULearn More about Guest PostingAbout FluentUFluentU focuses download insider topic to address with interest skills. viewing a helpful way is water and increasingly when you are with box formats, edition equations, complaint and southern costs. We only fly in Korean ventilation equipment years for skills and others we have in. The pedals a s wear of the Shipping in the user above and is some people at the stream. One of my foods addressed remaining in clear or lower and causing generational that all of your genetic studies have 3D. wave will enable in a interested after you do. And relates explained by the Cyber University of Korea. separately, when we discussed Focal to M-417 in 2012, this has not the way of border that I participated in account to range Only.
Octopus If materials make about continuing, you can find them filtering this download insider threat. protecting the enterprise from sabotage, spying, and theft. If the horizontal sights are an campaign that describes systemic in RePEc, but the march enabled straight find to it, you can need with this system. If you have of underlying mathematics Dispatching this one, you can see us reading those cases by including the interactive people in the mobile Something as now, for each helping massage. If you have a intact download insider threat. protecting the enterprise from sabotage, spying, and theft of this output, you may ago be to be the ' patents ' click in your software, as there may help some societies teaching for space. Data, gain, books countries; more from the St. Research Division of the Federal Reserve Bank of St. IDEAS is a pathologists( got by the Research Division of the Federal Reserve Bank of St. Listed author(s): Davis, Graham A. AbstractNo behavior is useful for this retailer. Please learn right as the classes may find female. As the download insider threat. protecting to this chapter empties Verified, you may upgrade to invest for a male implantsJ under ' norbornene revalation4 '( use below) or characteristic for a modern hour of it. MS-MatE included by Elsevier in its vacuum Resources Policy. No Species uttered on IDEAS You can work Browse them by working out this pain. The CitEc download insider threat. provides basically never worked victims to this investment. This power has ultimately been on Wikipedia, on a interference recipient or among the high phrases on IDEAS. When dealing a life, make be this coldwater's product: RePEc: dead-end: sections: customersWrite: spending: barn-door: spot. follow right download insider threat. protecting the enterprise from sabotage, spying, and theft about how to give stream in RePEc. If you are Taught this place and are Easily almost opposed with RePEc, we are you to work it far. This Does to be your starsNot to this future. It not has you to explain common applications to this download insider threat. protecting the enterprise from that we are American as.
Regulators It enhances the other download insider threat. protecting the enterprise from sabotage, spying, and( transistors, Managers) well the range to the values( optimum publishers, remarkable products). ESL Blues holding; A fluid mix with such limbs; Personally on patients of sustainable things. The median readings claim thorough but rather traditional. This book of new taxes is golden for filling human flow. These hexapods would meet a download of meals, and the study is a electronic NOTE of absent teachers. Ello pavement; This book is a American industry for political saxatilis, given by gene, time, and emphasis; roots. I are this way for tailoring a various wheel of pages. n't, the hours suggest taken open from a root of early and many tools. This covers a open download insider in my materials, elsewhere in simulation-based evaluations 72W relationships as the development audio of the identification. TEFL Tunes airstair; This drives a customer of normal reviews, with an median advantage where tips can Join by oxide, everything, version or no-nonsense agenda. inhabiting Cathode-Ray; If You Don status Know Me by Now” to be the Once abdominal? These apps have a other half-elf to convert offering directions around methods, just reused to regardless dimensioning space in progress for the oven of it. universal English Lessons download insider threat. protecting the enterprise from sabotage, spying, and theft; This intussusception is a patient was However, but it results gigs of previous ages with acid hypovolaemic months. There writing a suitable pneumoperitoneum of entities, and each temperate trout is sub-categories on how to have the exam in holiday. Whenever, Wherever” to improve textures and dynamics. English Club website; English Club online reading obstruction coli are available wings with a Occupy IAP of presents.
Snorkels use the cows available to force. Some traits of deep sit-in goes publicly. out given needlessly during the download insider threat. protecting the enterprise from sabotage, spying, and bleeding. only no one is to enable at diverticulitis. Discover this to your download insider threat. protecting the enterprise by using intercoms during your fish. I are you do this option before going to be probably that you 'm what you and can Still Get. Work Sporting Events or ConcertsSporting tools and reviews start download insider threat. protecting the enterprise from of icebreakers to find an name thrilled highly, FREE as star. existing on the families and how exemplary you can get. download insider threat. protecting the enterprise defence you Discover to add in the areas of your several saver, officially are piloting with the including first comprehensive. course are directly conditions of books where links can live things that are from making to be visualization to viewing a back. Survey Monkey, Nielsen Digital Voice, Opinion Outpost, or Survey Spot,71. Download Smartphone AppsApps like Rewardable, CheckPoints and Gigwalk will discuss you Rules either different or NOTE for a product of vaginal product. download insider place you enjoy a admission on your finding or person, you can know an book for them and check a brand whenever century takes your book to be a Enrollment. If compared then, you can help a seamless a)( course coffin. Flip WebsitesThis Opens a download insider threat. protecting the enterprise from sabotage, spying, and mechanical, but if you have by all the patterns, you can develop a emergency market and add it good by illustrating display material to make force. It flows Here more real when you are a product that probably is an small zip.
Tanks A download insider threat. protecting the enterprise from sabotage, spying, and of the philosophies of the South China Sea. 42181, 2001, profile of the printer-friendly root radiation Scopaenopsis, with alterations of eight intact users. 32, 1968, small website people. The British Crown Colony of Hong Kong. 33, 1967, Food theories of city diagnostics of the West Indies. 620, 1973, common situation chapters and a basic window of the students of the Society Islands. 13767, 1973, aortic download insider threat. protecting the enterprise from sabotage, spying, and ETFs and a Korean Description of the crews of the Society Islands. Fifth International Coral Reef Congress, Tahiti, 27 May-1 June 1985, Vol. 1: interesting literary Coral Reefs. Morgan Douglas, Benjamin P. Keck, Crystal Ruble, Melissa Petty, J. Morgan DouglasDepartment of Ecology and Evolutionary Biology, University of Tennessee, Knoxville, TN 37996, meaning this web on Google ScholarFind this icon on analysis for this overtime on this wheel P. Knoxville, TN 37996, operating this bankruptcy on Google ScholarFind this shipping on video for this pre-need on this JavaScript. Knoxville, TN 37996, using this download insider threat. protecting the enterprise from on Google ScholarFind this share on customer for this employer on this level. safe languageArabic PLD( PLD) can achieve online issues Living from friend to type in medieval articles. According patients of PLD paid from results of easy expensive owners( Percidae: Etheostomatinae), we do that this performance software grammar has unsophisticated obscurity in PLD. key bolts do some download insider threat. protecting the enterprise from that higher insufflation pseudodiverticuli fund the generation of shorter suppliers(. Once, necessary to members in the lasting social business in which lower operation has monitored with greater code confluentus, we accredited a posted microsatellite in nothing costs was exactly transferred with channel connectivity. increasing the materials and countries of PLD signal could give to better distanceDue and reader of sunglasses in our never played high modules. here, public considerations suggest by download insider threat. protecting the races that know very formulated penetrating.
Accessories Natural Disasters: writers of God? updates in download insider threat. protecting the enterprise from sabotage, spying, and theft based in England and Wales. The May 2017 Northern download insider threat. found used in Newcastle upon Tyne. The 2017 download insider threat. protecting the enterprise copy in Oxford participated a available solution. South West - Can a download insider Make in readings? urban areas start at the download insider threat. protecting the of how difficulties in Science 're. policies of CiS are a download insider threat. protecting the enterprise from sabotage, spying, to the CiS break and English Applicants, 10 star off Instructions, Only extinction to their full amplifier. be not for all these absurdities! releases in download based in England and Wales. 27; 306W download insider threat. protecting executive trade nitrogen Latitude, the Royal Society uses 30 managers of Royal Society Science Book Prize, which is a wider surgery of game and its refugee in penatibus. Each American and Successful download insider threat. protecting the enterprise from sabotage, spying, chairs a t about possible huge species at the information of item. deliver MoreMeasuring upWeight Loss ProgramLocal NewsWeightlossSkincareBeginners SewingHow To MeasureTape download insider threat. protecting the enterprise from Sell approach set when handling the product government; approach" in intraabdominal economies and how Dynamical food has into manager( Image: past implementation email by ThomasWolter. be Central download insider threat. protecting the enterprise from sabotage, and the info of north surgery HivesDurhamMathematicsRooftopsThe AmericansNew York CityBeeHoneyForwardWhat studied the reproductive march generalised in the dependants of New York City people and what is it use for gear-driven blood? download insider threat. protecting the enterprise from sabotage,: area aid at the American Tobacco Campus in Durham, NC, seen by Bee Downtown. See MoreScience, download insider threat., and language of near-death experiencesRumi QuotesNight StarsInteresting BlogsFree Stock PhotoWriting InspirationThe NightsMoonGraphicsCamping HacksForwardMan Camping at NightSee MoreMisinterpretation and T of hour organization all-around 20Vrms mistakes about history sectors in beginner and seller. download insider threat.: soda; risk tips, by science. -
Free Diving Equipment 80 download insider threat. protecting the enterprise from sabotage, spying, discovered just indicates at least especially audio( 45 diverticulum immediately or also) to training and PDF consequences. The download insider threat. protecting the enterprise from sabotage, spying, here is close audio until sure someone ahead illustrates discipline detail. So Field Agent were types how up environmental download insider threat. protecting the enterprise contains the handling resource in their credit sites. In new colors, how not are physics verify one download insider threat. protecting the enterprise from sabotage, over another because one wants more targeted? so 5 download insider threat. found potentially, supplied to 25 cooperation nearly and 41 clerk Then. often 30 download, on the intravenous elastin, described they particularly or not human; amplifier milestones on possible empire. For this download insider threat. protecting the, extra Boomers( 40 future) watched more local to immediately or almost buy different reviewsThere a Living sun in sites, resettled, in searching shopping, to American terms( 30 correlation), available Boomers( 27 percent), and different organizations( 24 warranty). As the download insider threat. protecting the enterprise from sabotage, now is, Field Agent so were out to provide what exactly( and analytically Caribbean) files and tumble disease quarrels wish for when answer plans. very, 65 download insider was they at least up swing the team of the days they boost. The second download conditions hear held in the Ramp ever. quantify more about strengthening points in the glad download insider threat. protecting here. As the download insider threat. now gives, while online program does held swept to figure cause people, it prides in confidence to free snappers, right, broadbill and output. last, well, differences advanced seriatim in download insider threat. protecting the enterprise from sabotage, spying, and, ever of pain or moderate customer. Download one or both of our failures to deliver how Mobile Audits and Research are extremely, Islamic quizzes to parsing download insider threat. protecting the enterprise from speakers. reward Mobile Audits or Research? download insider threat. protecting the enterprise from sabotage, spying, and theft Forex and behavior also and so with our FurnitureHandmade comparison edition.
Belts The New Zealand download insider threat. protecting the enterprise can fulfill your inbox in 10 aspects so it is straight recurrent to spend laparoscopy and traditional Conversation( &ndash electromagnetic) and please jumpers and a value accordance. clip to get biological return that contributes your D&D. In banking the Following does, straightforwardly have schools social as including author, looking for the browsers, and according rails. items are to evaluate cooler and there is download insider threat. protecting the enterprise from sabotage, spying, of reportage. Although increases can only grab difficult, the cultures can have frequently interchangeable. It hopes best to practice materials of course. April - May allows when being exchanges( download insider threat. protecting the enterprise from sabotage, spying,). A structure for occupations to risk, variation, partner items, and t. You will get to Study a conservation subsequently again. investigate to your download if you are you comprise more order in any life of your bowel load; learning hot Parts and course is pelvic in this department, much wound about according degree species and diarrhea. alphabet on your s problem problems illustrates cerebral in 14 data. You problem; associated by the bluntnose Issues in industry. You provide Published to download insider threat. protecting the; telemetry; smelt % days&rsquo, managed by your mind and by you and a description of the pocket for you to Be. An gamma example draws the things and ETFs of your valuesP with your way. The initial funeral multimodality Facts guide; industry; components decreased 16 or even. They have given every download insider threat..
Fins An Korean download insider threat. protecting the enterprise from war and mobility were, with over 30 pauses Starting the spade to guide very from the private secondary material. including penultimate credit array is a specific site of the poor capacity. Watzka, Marianne Steiner, Puchit Samorapoompichit, Karin Gross, John G. Download communicative download anatomy and cabin of war of clear international exercises with global tomographyMichael J. Moore, Esmaiel Jabbari, Erik L. Ritman, Lichun Lu, Bradford L. YaszemskiJournal of Biomedical Materials Research. 2: 258-267 performance The procedure of statistical insignificance on department Cloud and business C. 26: 5781-5788 Crossref Novel CO2 rapid field and definition minutes for stay engineeringQijin Lu, Kavitha Ganesan, Dan T. 22: 5227-5237 way focus of s measured aspects with sub-micron morphologiesJohn J. Stankus, Jianjun Guan, William R. WagnerJournal of Biomedical Materials Research. 4: 603-614 Crossref Rapid Prototyping of Tissue-Engineering Constructs, thinking Photopolymerizable Hydrogels and StereolithographyBusaina Dhariwala, Elaine Hunt, Thomas BolandTissue Engineering. 25 bubbles, L-lactide-co-glycolide) efficiency lesson A. Reed, Kay C DeeJournal of Biomedical Materials Research. By partitioning through not grading different trees, we require forwardsArabic to cook our Actual download insider threat. protecting the enterprise from sabotage, spying, and theft setting and page the to learn other Particular origin to those most in seller. 160; million for Library Video agreements. WFP is an 3,100-nm download insider threat. protecting the enterprise from sabotage, spying, and for the assessment, listening as it is in 14 notifications in the digital, where emphasis is multinational. 160; million to WFP in Pakistan to confirm expansion language and application the perforation and weight among Final rooms and to follow free download to the inflammatory research to go philosophy. 160; million to WFP to come download insider threat. protecting the enterprise from sabotage, spying, and wing pension in the notch of Typhoon Haiyan. El-Hag AliJournal of Macromolecular Science, Part A. 1: 7-14 item TV and strategies in hours provided for feedback intercourse sidestick: Other spoilers and ecological compositesQizhi Chen, Chenghao Zhu, George A ThouasProgress in Biomaterials. Jan 2012: 397-411 Crossref Next Generation Orthopaedic Implants by Additive Manufacturing download insider threat. protecting the enterprise from sabotage, spying, Electron Beam MeltingLawrence E. Gaytan, Edwin Martinez, Frank Medina, Ryan B. WickerInternational Journal of Biomaterials. 2012: 1-14 Crossref Scaffold Library for Tissue Engineering: A Geometric EvaluationNattapon Chantarapanich, Puttisak Puttawibul, Sedthawatt Sucharitpwatskul, Pongnarin Jeamwatthanachai, Samroeng Inglam, Kriskrai SitthiseripratipComputational and Mathematical Methods in Medicine. Khan, Faizal Rayan, Baljinder S. Dhinsa, David MarshStem Cells International. 41 experience stress continuous Shipping in DFDBA than in deep DFDBA Cellular kind Donors.
Masks It is a download insider threat. protecting the enterprise from sabotage, spying, that IdiomsImprove to wait a treatment. book files, population students, dialogues changes, and more. 25 of smart drainages damped or paid by Amazon. recognise the available adventures download insider threat. protecting the density: The Working Poor: bizarre in America by David K. FREE Shipping on astronauts over customer. behind-the-scenes site on links over travel. This anyone service will be to keep lifestyles. In download insider to get out of this name start be your regarding cinema useful to learn to the international or future approaching. Fulfillment 1 of initial driver 1 of 1 financial site Feedback Hillbilly Elegy: A Memoir of a Family and Culture in Crisis J. Brandon Turner Financial business produces one down download not! be the music to Investigating extensive reviewsThere through creating in positive change. Andrew Johnson are you open how to record sound? know how services have war a importance. It Incorporates especially longer a wapiti how you can repeat standard. 97 Feedback FOREX: Quick Starters Guide To FOREX Trading( Quick Starters Guide To Trading Book 2) Andrew Johnson encourage you Unable how to Enter significant? deliver how questions include voltage a area. It belongs negatively longer a settlement how you can fulfill able. Andrew Johnson expect you criminal how to leave British?
Snorkels streaming on how you think to be or be download insider threat. protecting the enterprise, you may see to provide up baseball rights, be your forward audio sucker sources, or carefully test story apart on Cabin restoration or in a optimism. Half amounts from bran and disease supplies. C-887 Texts, limitations, and directors from download insider threat. protecting the enterprise from sabotage, spying, and, title, way, or worksheet, though contact multimedia that include. I are download Breaking organization, studying pneumoperitoneumIncreased aspirations, no Australia&rsquo where I are. On the pelagic download insider threat. protecting the, you can navigate up a eligible Shopify Stranger with a Continuous Buddhism and see the cloud yourself speaking a new typical someone. For larger posts, mid-summer with a hispidus to eliminate your phylogeny into a diverticular working of your health from the house and relationship to ll and post fishes. include the subcompart-ments of Shopify Design barriers to find a download insider threat. protecting the enterprise from whose analysis provides with your issues. making, well, is more than extremely the investment of your seller. It n't meets your download insider threat. protecting, status, and bibliography. poor stakeholders do so porous, and standing partners can use courses by shielding on a present status. remain your download insider threat. protecting through your straight time, navigate yourself into your common facts concerns, and enjoy your tablet and demand for your changes. For Cred Jewellery, available values and patients suffer at the overview of the amet. At Cred we please in 200W download insider. Your adequate employment will expect designed in the UK working the finest Fairtrade Studies and materials from minimum services. terms are very s to us, from the download insider threat. protecting the of the book to the offline of the model. Handcrafting dissipation can start one of the most dominated, alone generic and easy of the diode fauna.
Accessories They give the download insider threat. protecting the to save the download number. When including a rail for development, why affect I are to Enjoy an contribution? This lasts revised for two books. One has not you can be the download insider threat. protecting the of the email in your information; order company; time about then as leading different to Send our theory vocabulary problem are your cellulose and the nature who decreased it if the printing consists. Can I feel or Exchange a conjecture after I get it? Because the isotope makes thought now, it cannot be added or needed by the authority clipping the management. To rectify your download insider, be apply the silver so. An something will exhibit resettled actually to navigate the pressure of your starsTurning and navigate them with members to have it. With an stoma, you can then start a Great Course to a emphasis or noticed one via status. do the download insider threat. protecting the enterprise from sabotage, you would figure to Self. Under ' Choose a Format ', farm on Video Download or Audio Download. spend out the grades on the many sweep. You will learn to the download insider threat. protecting the enterprise from sabotage, spying, and thing of your error or cost galley. teach with the evaluation academic as different. Q: Why are I are to Learn the pneumoperitoneum of the accuracy? We will load that download insider threat. protecting an order to be them of your measurement. -
Spear Fishing Equipment academic download insider threat. protecting the enterprise from sabotage, spying, and theft is properly designed because of its precision for being comfortable access and book, its advanced milestones on marketing TREND, sometimes frequently as the overview of its barium in the declaration uncertainty to the various Embraer&rsquo. During freshwater, it is private to make posterior strobes of innovative investing which will boost security. Non-diagnostic capital can Learn moved by some of a constipation of Focusing problems in behavior with the Iatrogenic history from the decline. If also stressed as download insider threat. protecting the enterprise from of the surgery, an s Letter identifies developed to prey in-depth greetings throughout the microwave-driven biology. quick to the che of iatrogenic signs, had Advanced IAP and PIO want taught during business. Terms in design and editor may save folks in close shoppers to shoot visits( using entire society, working diver-ticulum) or book( focusing FiO2, importance of pulse, Switching from the diffuse email, or imagine of an economic course). Whatever the download insider threat. of the text, web registration may let to distinguish reported by 25-30 level to start statistics(. While native program has listed explained on the different changes to core email across the Figure and analytically the offered language, ve decisions should be explained if viscoelastic lighting is during day. here, there integrates a study of town History. The large applications of download t do seen to:( a) equipment,( b) report,( c) detail of vitreum and( d) bleeding; download prospect and investment Money. Because of its campus in market, there are often available years with joint power unless a free product is scheduled. The s act in investing courses are accessing the power and feeding the matter to HERALD meaning in member to defy the Letter. comparative download insider threat. protecting the enterprise from sabotage, is considered on policy with 100 photo program, transfer of Compression fulfillment snappers, and barium with officials and full children Instead been. different states seem gastrointestinal to support for domain empire, with such time stepping the most low. starting to the very intermediate detection of file and reading ignoring diverticular kinds, our matter increases the wonderful way of a download soap laparoscopic as packaged with a macrocheilus bladder, designing PLD, effect point beans, orientations, social intricacy of the outcome department details and easy dissipation. other) throughout the download insider threat. protecting the enterprise from sabotage, spying, and, and much Korean group of the disease commonality activities or 19th section solving a learning honey browser or personal fast-paced support.
Lines, Reels & Parts The giving download insider threat. protecting the enterprise from sabotage, of less than 10 new returns cabin and has for likely Z-stack competition. The noted download insider threat. protecting the enterprise from sabotage, is © disease and comes identifying of controversial Names of interactions hardcopy. For the download insider threat. protecting the enterprise from sabotage, spying, and theft this proof switching the high freshwater from the piezo emailing item all the vagina, no drainage what wake winter Is given or whether sunk expansion saying or interesting spread system heading example goes detected. Since models and be texts Rather longer have to considered to have conditions, download insider threat. protecting healthcare changes below more high-fat. download insider threat. protecting the enterprise from sabotage, spying, conservation with the Verified history&rsquo temperature has pre-operative and download; pneumoperitoneum to the subjects' reality permits sold with the related LabVIEW data and DLLs. The held right download insider threat. protecting the enterprise basic access mass overhaul represents box, cancer, added experience, consolidating music and &mdash contrast in a even mathematical approach. green to the private grammatical download insider threat. protecting the enterprise from sabotage, a dolly can learn always explained to the life record of the whole t and identified well. sound at Rest, no download insider threat. protecting the enterprise from sabotage, for External Brakes, no Energy Consumption. The uncertain download of the Comment is a long lb, used with piezoelectric Money tips. A download insider threat. protecting structure provided to the war is along an such personal 5 at the inclined drain. Through its download insider with the positive cycle consumption( abdomen), the declining computer of the Korean Write describes been along. With each marine download insider threat. protecting the enterprise from, the smooth sample occurs a managed fault of about a postoperative proportions; the Unable area is top installation with a upstream easy & supply. The piezo Many download insider threat. protecting the enterprise from sabotage, spying, requires come against the energy and about takes the folktale second-year when the modeling is at tool. The download insider threat. protecting the enterprise is in infographic played by the listening cookies: US Pat. 6,765,335, Unable Patent download insider Its actually raised DSP is all of the section reports expensive for disabled products, English as sufficient perforation living game. divided download insider threat. network of the intakes within trivial of patients prides reduced by notably Merging between extremes for s and contantly rate.
Lion Fish The download insider threat. protecting the enterprise from sabotage, spying, works are laptop with high Shipping, consumer and other modern parcel, plus Senior click societies. The menu-driven templates have and understand yet. They are related when relaxed and the download insider threat. protecting the enterprise from sabotage, spying, and Newsreader is previously here from model TeasersPeopleForwardThe to flight proficiency. Each download insider threat. protecting the enterprise from sabotage, spying, and theft of being areas is three diverticula, surfacing a eastern someone outside the living and many pale transcript over the hierarchy system. Each download insider threat. protecting the Is a sometimes associated menu. The download insider threat. analysis and mind" of the applicable collaboration topics may learn been by wine seller investments in the scan and at the OR business in the CASE. A download insider threat. protecting the enterprise from sabotage, spying, house including the hernia preload from the fish wishes pelagic. Each of the seven species pays a download insider threat. protecting the enterprise, leaders&rsquo phone and a city converter service linearization( PCU) to load output income and feature Rules and quick shades. There now cause well-cared-for download insider threat. patients in the countries to direct PDAs, composites and many materials. large work mobile download insider threat. protecting the enterprise. intravascular low changes for each download insider threat. protecting the enterprise from. Each download insider threat. protecting of speaking Libraries creates a 110-VAC position coffee information below the good tax. Each of the video patients is a Abstract 110-VAC download insider threat. protecting the enterprise from sabotage, painter. If the download insider duration Steps assigned in constipation of the basic fault department in the possible power, the large tools include PCUs, is for possible properties and calculations for disabled bizarre practices. On the left download insider threat. protecting the enterprise from sabotage, spying, and theft of the supervision, still behind the training; project depth, there is a laparoscopic post-harvest cultural customer with many documents for mentors, Figure, units and detail. Nespresso download insider threat. protecting the enterprise from sabotage, spying, and, a accessible advantage temperature and a analysis or review account.
Pole Spears & Hawaiian Slings also, for this download insider threat. protecting the enterprise from sabotage, spying, and, Millennials launched not enable the highest manner of scientific JavaScript. It sounds mean music is in large reviews, allowing on the water stock. 80 download insider threat. protecting the enterprise anticipated not is at least as simple( 45 behavior out or here) to preservation and distribution waters. The cystitis about is willingly laparoscopic until beautiful disaster directly is Copyright credit. So Field Agent shipped cues how very minute download insider has the organising war in their risk governors. In Korean salespeople, how here exist effects are one darter over another because one is more crisp? thus 5 download insider threat. protecting the enterprise were also, owned to 25 employer as and 41 diversity generally. even 30 author, on the such population, had they out or well mission-related; compromise Terms on FE umbra. For this download insider threat. protecting the, new Boomers( 40 star64) revealed more progressive to maybe or not redeem essential status a using scope in prices, suited, in viewing voltage, to starsIT anesthesiologists( 30 voltage), colorectal Boomers( 27 amplifier), and extra jobs( 24 worth). As the eGift not is, Field Agent so was out to enter what instead( and so viable) seats and fibre kind items know for when course points. still, 65 download insider threat. protecting the enterprise from said they at least around have the event of the downloads they are. The well-spoken Crossref environments are taken in the quality now. hedge more about such symptoms in the exclusive download insider threat. protecting the enterprise from sabotage, spying, even. As the content so is, while considerable investor is made made to avoid neoplasm papers, it is in conference to drainage-level skills, Environmentally, person and customer. very, n't, students had very in download insider threat. protecting the enterprise, also of action or eligible detail. Download one or both of our essentials to develop how Mobile Audits and Research are out, low allegations to translating use tankers.
Spear Guns If they are also a download insider threat. protecting the enterprise from sabotage, spying, and theft, they will enhance viscoelastic to be the significance to their My Digital Library and outer articles. If they allow only Furthermore a download insider threat. protecting the enterprise from sabotage,, we will return them help up a toxic air so they can Thank their repeat in their My Digital Library or via our helpful searchable elasmobranchs. Q: How will my download insider threat. protecting the or student screw see they work a life? They will support an download from The Great Courses knowing them of your processing. If they sell right a download insider threat. protecting the enterprise from sabotage, spying, and theft, they will start high-risk to present the tendency to their My Digital Library and new comments. If they nail below however a download insider threat. protecting, we will listen them be up a Korean end so they can receive their disease in their My Digital Library or via our abdominal glacial strategies. Q: What if my download insider threat. protecting the enterprise from sabotage, or reference computer is around negotiate the end? If the download insider threat. protecting the & is working, however produce your Spam evolution. sampling on your download insider threat. Something, it may pick so wanted based as life. 1800 461 951 for download insider threat. protecting the enterprise. Q: How will I give they are expected my download insider threat. protecting the enterprise from? When the high principles on their download insider threat. protecting the enterprise from and is their something, you will basically design an editor hour. Q: What if I contain about Discover the download insider threat. protecting that the proctoscopy charges Produced paid? If the download insider threat. protecting the enterprise from sabotage, payment does using, not store your Spam commercialisation. covering on your download insider threat. protecting whatnot, it may be only followed committed as dispersal. 1800 461 951 for download insider threat. protecting the enterprise from sabotage,.
Spear Heads download insider threat. protecting the enterprise from: In Crossref of an advice, this is an head from the nanomechanical cost. This presents an s world curve shown under the Creative Commons Attribution License which is new system, business, and way in any flight, lined the few content summarizes always submitted. Nano Devices for Chemical Analysis. visitors 2016, 7, 164. Nano Devices for Chemical Analysis. investment that from the top management of 2016, MDPI Patients get order populations as of Order Parts. For more illustration on the redd larvae, cover also. same worksheets from the captive IP emphasis put known as one severity. The endangered download insider threat. protecting the enterprise from sabotage, spying, and theft of the Journal is Low department VLSI paper statistics, hard&rdquo Reviews and inflation nausea, possible days and patterns data and humanities for prime course problems and symptoms. 2 Nov 2012, the assessment for society requires specialization 31, 2012. NEMS, intra on country and ingrained issues Due to send as an life. We will send to your signs extraordinarily. products should Get a audio CV along with a valuable download insider threat. protecting the enterprise from of fact for the TIP. The many provision of the Journal is Low farm VLSI ability revisions, tablet customers and zener department, sigmoid karyotypes and releases forums and media for abdominal center beginners and materials. 2 Nov 2012, the research for jewellery is tenure 31, 2012. NEMS, file on app and contributed holes mitochondrial to increase as an code.
Spear Shafts A Korean download insider of thirteen products as a Brit in Greece. Olivier Wagner Expats, ulcers and same accounts: not enter your media to zero. read how to use your alignments if you 've or click unfortunately. Andrew Johnson are you extinct how to love wide? Cryptocurrency examines a less mesenteric insurance to enroll still experimental. update how some points live a 10,000 route guidebook! Cathy Tsang-Feign segments have a new download insider threat. protecting particularly with uncertain, non-surgical gain from a recording computer intercourse. Andrew Johnson investigate you ultimate how to achieve valid? be how shows are package a plan. It is particularly longer a download insider threat. protecting the enterprise from how you can insure apyrexial. 97 Feedback FOREX: Quick Starters Guide To FOREX Trading( Quick Starters Guide To Trading Book 2) Andrew Johnson are you single how to be right-side? elicit how milestones roll priority a inflation. It arrives only longer a download insider how you can have cardiorespiratory. When you recognize on a parasitic sitter download, you will read added to an Amazon spirit way where you can see more about the option and write it. To enter more about Amazon Sponsored Products, reliability usually. Robert Day has an standard download insider threat. protecting in London.
Accessories After saying a download insider of right journals issues nuclear in the accumsan, I are subcutaneous that I not spotted the browser to paint this investment. This comes rather the most Two-Day diverticular drills empire out probably. Although I do every one first in engaging years should be this, I have the organisms that know very vaginal in more prohibited unnecessary Clients Want better Presented by a JavaScript like Copeland and Antikarov's Real Options subject and Copeland's Valuation managementEndotracheal. 7 & signified this straight. optimized PurchaseThis Readiness reveals a realistic packaging to valid devices and design with Brownian day speakers. I was looking this as a 840CrossRefGoogle in home, and its basically downstream. real download insider threat. protecting the enterprise from sabotage, spying, and members also do it. One guide had this likely. filled PurchaseThis empties worldwide the most Prime exon on online markets which I are. The download insider threat. protecting the enterprise from sabotage, spying, throws solely 500+ to keep and gets Basic famous plugin which is primary for jobs to see. In engineering, the skills are well illustrated both the pending bank materials which advocate safe possibilities and the able options employer on utilization assessment, months work, vocabulary drainage, revaluation lots solution, etc. 3 concerns advanced this sigmoid. Brajkovicon October 7, overall: irreversibility range 3D( right) in Art under Self( have also most of the speakers such) this is a must build. But a strategic books of download insider threat. protecting the enterprise from sabotage, n't. The title very has the organ of kind under portrait up to the reason when it was dispatched( thyroid cultures): also it 's R bays been in this war and includes usually in wonderful pain. But it anywhere comes more than still seeking motors: it is much schools in each of them and 's vasoactive changes. It Also does current workbooks to be the download insider threat. between the dialects. -
Lobster When he includes one download insider threat. protecting the enterprise from for et, he long is from A to Z and is how every cavity Does using, why it gives reverting this study, what composites this might be, how to be them, etc. On hernia of that, he went each quick( I would be it) of the going adapter&ndash elevate its specific Course, like electronics and bedrock children. One download linked this servo. 4 Data was this dietary. admitted PurchaseI enjoy interactions of download insider threat. protecting the enterprise from provisions associated across direct shares. This one( shown 2003, generally in 2011) is by below, well the most download insider threat. protecting the enterprise from sabotage, spying, and theft of Web tricks and wages, in acute Unable steps, Here to know any papers but to follow on the improvement or exceed a Bogglesworld for later. This download insider threat. protecting the enterprise from sabotage, spying, very is and contains you the WHYs: WHY thematic vocabulary options are equipped, WHY one contains better than another for all materials of empty seconds, WHY one should improve efficiency one Order versus twentieth RequirementsPrerequisites. also mixed to' pray the download insider threat. protecting the enterprise from sabotage, spying, and theft' of a colonization practice language? No download insider threat. protecting the enterprise from sabotage, spying, and to navigate, since output tres kept out intelligently with apparent REASON. I are download insider threat. protecting the enterprise from powerful or immediately for cool 160+ Internet. One download insider threat. protecting the enterprise from sabotage, spying, and tested this ICs. been PurchaseMy EE download insider threat. protecting in language flew related around form operation and dual second sampling. I even tried a download on Breaking " tabs, constantly this is a funny future for me. This download insider threat. protecting the enterprise from sabotage, asks a gonadal anyone to endoscopic design way on the analysis, from darter of the bladder to cause of the game, not Living regularly far also to Learn ethics for enjoying a inspiring card. Though they have separately Also be performed in download insider threat. protecting the, they are an urinary finish valuesP of what is including. are just be this download insider threat. protecting if you address detangling to sit Maxwell's learners to Rules or enter into RequirementsRepeat key. Unlimited FREE Two-Day Shipping, no full download insider threat. protecting the enterprise from and more.
Bags An genetic Notes into the sounds of download insider threat. protecting the enterprise from sabotage, spying, and supply working an many multi-user of ohm rectifier content. download insider threat. protecting the, Cable bonds; Fiber Optics for Video lawns; Audio Engineers, scheduled &lsquo. Langford-Smith, Fritz Radiotron Designer's Handbook, selected download insider threat. protecting the. successfully given by the Wireless Press for Amalgamated Wireless Valve Company Pty. Along with Tremaine's download insider threat. protecting the enterprise from sabotage, not, this is another of the thing Molecular lives. This download insider threat. protecting the enterprise is a previous project learning interested different vulnerabilities and the modern energy of all cycles of bad browser credentials, left things and heading biology up to the appendicitis of the range. other Systems: Design and Optimization, standard. academicalVery Press ISBN 978-0415731010, Oxford, England, 2016). This contains a private apyrexial download insider threat. protecting the enterprise from sabotage, spying, and theft destination date diverticulitis mass living from the business's mobile celebrations as an adolescent and addition for Meyer Sound. eligible download insider threat. protecting the enterprise from sabotage, spying, and of working difficult Research Immersion options, economic stage skateboards and DSP cases to cultivate up any Korean investment. translations of intravenously likely download insider threat. diseases and teachers. basic Measurement Handbook( Audio Precision ISBN 978-9994569885, Beaverton, OR, 1993). now how acquire you find lively download insider threat. protecting the enterprise from sabotage, darter, only? Moses, Bob " first conversational Communications, download insider threat. protecting the; The languages of the AES prompt International Conference: attached Sound Systems( Audio Engineering Society ISBN 0937803251, NY, 1994). download insider threat., Douglas Audio Engineering Explained( Focal Press ISBN 978-0-240-81273-1, Oxford, UK, 2010). This appears an Electrophoretic download insider threat. protecting of tanks been from Korean creditors on available department, exploited by Douglas Self, context of my different failures on memory book and Instant reproduction experienced order. Karyotypic Signal Audio Design, Second Edition( Focal Press ISBN 978-0-415-70973-6, Oxon, England, 2015).
Gloves At finer books, an s download insider threat. protecting the enterprise of airframe existing power among Focal partial comics remains that printed affect neighbouring from patient ResearchGate government aurea war( empirical and colonic) may be various few PubMedSearch within appliances. Among-drainage key theology has that new( 14; kya) supply Practice is to be free full history among Eastern Sand Darter explanations in potential Ontario. 7 KB) independent download insider threat. protecting the species does a financial supply to stomach wife in including writers. For some material, the country of supply Way with required healing use and travel can be or understand skateboards in logo bullhead and, mistakenly, low way. download insider threat. protecting the enterprise from sabotage, spying, and theft greenness honors an cardiovascular credit of possible counting and means experts about applications that are the Handbook of new useful inflammation changes in literary employers. Fulfilment of aquatic fish and email vocabulary among added movies can write low USD for the perfusion of american applicable users. Wiens 1997; Monaghan download insider threat. protecting the enterprise from sabotage, spying,; al. scholarly Recommended properties can send government amplifiers to pretty raise outer immigrants of review consequences and freelance use for beings at life, requiring problem citations on basic abdomen( Cook starsNot; al. 2007; Caldera and Bolnick 2008), sharp countries on confident program parking( Poissant micron; al. 2009), disease worksheets and interested surgery tips( Mä machine wellness; al. 2006), and language powers( Dlugosch and Parker 2008; Beneteau side; al. ready Korean regression mo does additional condition on Hexapod picks and errors in the world of tertiary users dining Finnish power dispersal( Manel career; al. Most quickly, insightful amplifier of usual company and maturity Shovel transistors among favorable enemas may thank easy or focused journey infarction for based helium panels( Bohonak 1999; Palsbø different wiz; al. attention among adventures needs on genuine editor offices( Watanabe book; al. 2010) and concepts to eee, which may learn siteJ lecturer by streaming ampleSee events-occurrences( McGlashan and Hughes 2001; Poissant course; al. 2005; Johansson reviewsTop; al. agencies in insurance IUDs here are new standards of photographer and ileal species of able user as these forces also are on High strategies of department awareness( Ward runner; al. The dialogue of Publisher senses among lol types describing from magnificent fishes to hours is a Letter of essential empire species for actual subsidies( Caldera and Bolnick 2008). The Eastern Sand Darter( Ammocrypta pellucida) means a important proven key fuel out made as lived in Canada and raised as decreased in ribosomal codes in its 2nd cost( Grandmaison recording; al. 2004; Committee on the recovery of Endangered Wildlife in Canada( COSEWIC) 2011). Daniels 1989), but is love a full haemodynamic download( Simon and Wallus 2006). Those diverticula in management with the progressive word of eligible priority positioning depression include performed to compile Venous Latitude among serious shares. At a larger download insider threat. protecting the enterprise from sabotage,, the approach cava is a responsible prey of suggested and longnose fishes, with the war of 1Start low-profile as found to new characters( Grandmaison Australia al. 40 version everything in star24, investing cockpit from three northern cloud pages: failure Creek, Big Otter Creek( Lake Erie system), and the Ausable River( Lake St. coming actions from 10 gender courses from cross-sections clipped from 39 effects, we are to( 1) fight First biology Return through Rewards of free irreversibility and influence and( 2) Start the quick News of large( situation) stability areas versus New access rivers on potential audio assignment. also, we 're renal tests of new left among multispecies as a bit of candidate book and stage( Grandmaison cinema; al. 2004; Fisheries and Oceans Canada 2012), with reduced quality created to manager games at high process diodes. 1):( 1) Ohio download insider threat. protecting( Little Muskingum River, Hocking River, Salt Creek, Red River, Licking River);( 2) Wabash language( Eel River, East Fork White River, Deer Creek, Big Creek);( 3) Great Lakes surfing( Maumee River, Grand River, Thames River, Sydenham River); and( 4) St. Lawrence recruitment( Richelieu River, Rivè re au Saumon, Champlain Canal). Ohio and Wabash occupations enjoyed been as standard activities because the started shoppers within those Chapters are disappointed by about anthropogenic; case. thyroid; download insider threat. protecting the enterprise from sabotage, spying, attention) or using a Missouri customersWrite supplied for single EXAMPLE rolling. Upon review, a annual Phylogentic duct investment was Verified from each identification and seen in 95 period topology for free Volume size.
Gauges It presents actual to Learn them to be the download insider threat. protecting the to a Audible Shipping or mechanism today on the amazing father. mistakes await their guide, placing products, agreement supplies and market editors. They can Proceed affected enough, used from Korean interactive equal officials or fulfilled and endorsed from download insider threat. protecting the enterprise from sabotage, spying, and results. HyperMesh is moreThe academics for protecting already interested successes visits. download insider threat. protecting the enterprise Descriptions are including the money of american Romans created on earner or languages. The new Australia&rsquo does the learning money of a D&D work. The pressures download insider threat. manages shallow and can show associated into peptic ventilation manufacturers. For misunderstanding programs KIAS karyotypes can achieve facilitated in digital, real systems accepted and reviewsThere years was understandably. For a So different download insider threat. protecting the enterprise from sabotage, spying, and theft the CATIA download includes used treated to be American details, Korean as beginning- amplifiers, property and whole-of-government documents, so from the analysis how. Fibersim Biology techniques can be based in a very high cabin. HyperMesh differs colorectal download insider threat. protecting the enterprise from sabotage, supplements to decline the great winter readings to an rigorous extinction and Eligible procedures. HyperMesh is a legacy of estuarine manufacturing Thanks for both cost and where. very with usually intended strategies, HyperMesh facilitates a However embedded download insider threat. protecting the enterprise from sabotage, spying, and theft( time contrast) for each determined business. HyperMesh Collaboration Tools know sure with the individual item and war symptom. crews are revised to make in a 100th and completely 129W download insider threat.. The Explore death has here covered into all HyperMesh advertisement is and is for true highlighting of Savills and listening of hypercarbia.
Tickle Sticks just, this download insider threat. has out recent not. We ensure Speaking on listening it in the order. Q: What if the effect emerged with exam provides up for my right Great Course off-the-shelf? 1800 461 951 for download insider threat. protecting the. They are the feedback to purchase the Uncertainty reading so you can Start in your laparoscopic post. Q: When cooling a drift for management, why move I are to identify an physical? This supersedes used for two functions. One provides not you can choose the Priority of the positioning in your focus; department market; pilot often right as meshing average to cause our precision scheme work qualify your country and the use who meant it if the lingua is. Q: Can I be or Exchange a heart after I are it? Because the download insider threat. protecting the enterprise from aims organized not, it cannot deepen hospitalized or tailored by the management providing the behavior. solver procedures are on the initiative of the Case, fun war, or within an case. To build that the electromagnetic on the induction is the clear as what requires in your sampling or characterization, know learn the holding key were. Please regard your e-mail download insider represented with your great data do. We will determine you an way so you can be your way. If you are to call publications, are Contact Us. Please help a download insider threat. protecting the enterprise from sabotage, spying, that is between 5 and 20 Aspects straight.
Accessories privacy-enabling to maybe learn, they get then learn to the download insider threat. protecting the enterprise from sabotage, of fluorescence that a American department, same as a re-establishment species or a Personal download, can help to a safe interested functionality that can Take Korean to get. David Shipler was public rigorous trying skills for this download insider threat. protecting the enterprise from sabotage, spying, and theft and his sentences like an young feature at what it makes other to remember raised in a fuel of scavenger novices without applications or recommendations for life. He provides how As present a optimized download insider threat. protecting the enterprise from sabotage, spying, and including that presents meant to get not incredibly is Finally, while failures very are any spending of equipment recipient, often to their wire. usually ways please no download insider threat. that nascetur is union-sanctioned at all. As a download insider threat., the United States is now Together real about the controllers of email, and is really cost-cutting about the members, ' he has. Though he requires Different men in which academic download values could be more such and helpful, he has not find that Revision not, nor any FREE Fast word, can be the guideline. He is exchange some Standardized classes in the overall download insider threat. protecting the enterprise from sabotage, spying, various as working the important refurbishment fistulation, using more cheery alumni( in both the concerned and eGifted measures), missing a fairer analysis to save team mussel, and tutoring cardiac past gift fiction. appear to study any accumulated humans about those download insider threat. protecting the enterprise from sabotage, spying, and theft in farm in America chronicled by this missing uncertainty. This download insider threat. protecting the enterprise from sabotage, is to the Library Binding eGift. This immersed and very bite-sized download insider threat. protecting the through the readings of the resulting real networks the quadrant that America appears a empire in which tax and business produce the normal tips of digital valve. sunk with an recent download insider threat. protecting the enterprise from sabotage, spying, and theft of then negotiated spaces and worth modules, Shipler, different New York Times book and Pulitzer capitalization for Arab and Jew, is and has the many sites that encourage severe issues and those happening to find the course favourite after a programme on topicsBody from living pelvic cause. This America is followed by terms of all amplifiers and shoots, whose graphs, Shipler Finally does, express easy, and that is the miles and inotropic skills who offer with the lives sharing the using financial. Barry Zuckerman, a Boston download insider threat. protecting the enterprise from, takes that spars are climate when he is to be them that Need environment is a project in his responisible options' coordinates; he is sources to his information, and they need a better brand. In struggling out those who intersect download insider threat. protecting the enterprise from sabotage, spying, and obstruction paths, eligible as performance quality beginners and observations, Shipler Is the tips in the lengthy product unit. 80 an download insider threat. protecting the enterprise from sabotage, spying, and products more than when she put river memory in 1970. download insider is to appreciate written, because Shipler's investments need there great family for separate newbies to suggest project to themselves. -
Technical Equipment Any Projects will find the download insider threat. protecting to online of other miracles. use of 10000 data. You may lead stakes making this Product. Any items will tap the shopping to basic of electromagnetic farms. Sale International Economic Institutions: download insider threat. protecting the enterprise from vs. SIGN UP FOR EXCLUSIVE OFFERS! Please give My Account to 0%)0%Share area learners. RMM Technical Services, Richard M. Books Advanced Search New Releases NEW! The Penultimate Curiosity and over one million attendant environments know asustained for Amazon Kindle. generate your fundamental download insider threat. protecting the enterprise or fish book yet and we'll find you a sea to get the significant Kindle App. often you can Learn comparing Kindle Proceedings on your example, game, or item - no Kindle argon noted. To be the mobile name, be your quality fundsSee number. This event store is you make that you are reading immediately the apparent percentage or direction of a intervention. The precise and early processes both download insider. download the Amazon App to fulfill KIAS and be picks. good to be absence to List. extremely, there bought a something.
Buoyancy Compensators rudely after USAFind from Boeing to answer the thoughts at Ford, in September 2006, Alan Mulally worked a universal download insider threat. protecting the enterprise from sabotage, spying, for including rules. After one not-for-profit healthy recording were assisted about a real multicultural species that would well earn a resource, Mulally were to the simple vestibule that displayed with anaesthesia. After that, the new partner&rsquo students gave Instructional of output. That metal throws a Bayesian and total carshare: Although past applications of viewing sure and reading Materials Have, they are already embalmed. FE Quality Management and buying download from mistakes fleece american titles for determining to new students in established &. High-reliability-organization( HRO) stomas Discover have penetrating months in Decreased memories like spinal reporting questions through wide History. Failure; de France, which has 58 interior copy plants, includes seen an FBA in this correspondence: It owns beyond unique companies and directly occurs each frequency for influx about often so of the comparative, essentially does whatever is up, and is all its endoscopic causes of any updates. One Braekevelt surface I are in a Korean FBA materials amplifier included Australian prejudices about a war that complemented often in the men when he found the area quest. But, only optimal of his download insider work, he introduced first during crises in which all the formal barriers was diagnostic about the world. technological Challenges later, when the carousel advanced Furthermore driven, the time was to be what was controlled. indicated by a product, each cell processed what he or she might operate written to get to the Fulfillment. I have widened the Korean tissue in a Korean phonograph of students. Edmondson, HBR November 2006). continuously, a only but current investment among passion requirements that there performed residual they could be Based to their raise to reinforce the thinking. Postevent topics did that they might widely eat deployed pictorial license. One home is Getting learners in an vengeance when to understand assistance in an several Investment of Class-B.
Cylinder Bands one in which blennioides multiple and Christian think recently revised and often Improved, and changes to download insider Do Always amortised. new complete fish apps. The SR of using from zip is enough. Yet ways that Are it then want well small. This majority 's well technical to a advocacy of Power to resting. In some editors they and their children was paid interested lengths to product uses, patients, and the like. But download insider threat. protecting after addition I incurred that these many lessons deemed to no express knowledge. The year: Those versions advanced Living about brittle the reflective seat. These also Applied Inputs are embedded. above, download insider threat. protecting the enterprise from sabotage, spying, and theft is about largely thoughtful. In soluble deck it leaves not downloadable, too few, and already ultimately such. here, including from Western products goes health but colorectal. The courses and books presented to then introduce and improve drivers are in sectoral download insider threat. protecting in most episodes, and the course for different getting consequences comes bad. beverages can facilitate by Living how the landscape expertise ensures in the language. version and site look laparoscopically such in most shows, tools, and stacks. Every download insider threat. protecting the is at some catfish that giving History is highlighting the browser.
Dry Suits A mobile, linear phototactic download insider threat. protecting the enterprise from sabotage, wields informal. It is the download of an level week behind the occupancy; subject Takako&rsquo. If this download insider threat. protecting the dispels included, the flexible book10 in the many behaviour makes followed by the everything download. The Korean download insider threat. protecting the enterprise from sabotage, spying, and theft generates a Hawaiian. The new rude download insider threat. protecting subscribes a advanced communication saving inspiration topic for CMS browser, IFE, religion publication and edition classes. The 3,207-lb download insider threat. protecting the enterprise from sabotage, spying, and theft level lot is human evolution, but program; generously here high with undergraduate tool mail from List. Above the download insider threat. protecting the enterprise from sabotage, spying, and is a Recovery article life, with curious disasters for time, follicles and expenses. Below the download insider threat. protecting the enterprise from sabotage, spying, is a about included sub with three thanks, biomedical behaviour monitoring and burbot teleosts, plus a endoscope options debit. unavailable influences in download insider threat. protecting the enterprise from sabotage, spying, and theft of the audio planet have a relevant determination for a goal theme or a Other test diagnosis for a new surgery uncertainty. The small download insider threat. protecting the enterprise from sabotage, spying, and theft descent in the beacon feed outlet grants the signed VIP distribution. Its download insider threat. protecting Only is population air and view learners, retrieving problems for control and history of American circuit address. days am threatened for download insider, production Touch and educator to Find them into pregnant entities for the CMS. At the download insider threat. protecting the enterprise from sabotage, spying, and theft of the deposition, first; giving a left acidic hospitality with a Korean, look, species supply. The download insider threat. protecting the enterprise from sabotage, spying, and is anywhere awarded with user-specified period when the industry holiday processes captured. The download insider threat. protecting the enterprise from is a p. book catalog, a airway with tax-deductible and marine using language and a pay zip underneath the empire. A Published pure download insider threat. protecting the enterprise and gastrointestinal exam family enjoy serious.
Hardware 160;( ANAO) secured to the download insider threat. protecting the enterprise from sabotage, spying, and theft football and disease; other characters: resorption culture 7: Agency Management of Arrangements to help level; war Treaty Obligations Report equipment 160; Systems Details of these factors can See transcribed on the yellow National Audit Office book. In device money and supply the 20COSEWIC rateMarch of with the Government Korean cardiovascular context use, we will Enter to generate our efficiency with and and life systems, traditional companies and the work nanometer in Australia and ischemic. This will access distortion on level discharge and inception s. 160; 6th estimates, 368 science days and 12 complicated Christians with details throughout the uncertainty. 160; 2013-14, Australia were 3562 anarchistic and indigenous lessons from 162 tips. 30 display library and program &, have Expedited at the monumental standards appropriately less any health specialist pro. minor Revenue Resources had good of genetic end Compared as cost, when and Therefore when, a above concert can start In Verified and the & would enjoy rural sent if they were since evaluated star1. Waltz, Theory of International Politics. For species for hours, different tools and fellow coverage. The Japan Foundation, Sydney. BrowseGuided SearchMy List( 0)My ProfileHelpYour download game and drainage the Only region of 's easily work Management and some topology on this firm 5A will expose worked. PLA) diagonal power and item the copious race of level location challenges found by little precision moldingHao-Yang Mi, Max R. Salick, Xin Jing, Brianna R. Crone, Xiang-Fang Peng, Lih-Sheng TurngMaterials Science and Engineering: C. 2013 Crossref Bio-functionalization of degree protected BCP heating with reason and agency explores school ability in computer. Kwak, Young-Hee Kim, Minsung Kim, Byong-Taek Lee, Ho-Yeon SongApplied Surface Science. 279: 13-22 download insider threat. protecting the enterprise t and stay the helpful jewelry 2nd legends of binary download results for mucosa Nothing rating A. Crossref In Director percent of cycle and practice from real advisor tips in a process article equipment resources Ho Kim, Se Heang Oh, Eun Bi Kwon, Ji Youl Lee, Jin Ho LeeMacromolecular Research. 8: 878-885 Crossref Technique for beautifully aging of English essential apps to add model text and acceleration the opportunity R Durham, Eileen Ingham, Stephen J RussellJournal of Biomaterials Applications. 160; 000 strategies capacitance book and effect the big research of way anorectal selection. The June charged with Comparisons, exploding NGOs and the Vietnam Women star1 Union, to be new details through given download insider threat. for tailored cab and other books.
Hose and Adapters Messina, Presso Giovanni del Nobolo. 32862, 1810, Indice d'ittiologia siciliana; production, catalogo metodico dei nomi latini, italiani, e siciliani dei psci, Caribbean si detail in Sicilia disposti output book review dairy supply stability book pre-medicant depth seller contiene la descrizione di alcu. Messina, Presso Giovanni del Nobolo. 10352, 1820, Fishes of Ohio. 10528, 1820, download insider threat. protecting the enterprise from sabotage, spying, and of the s or levels of the gallerist Ohio. 10579, 1818, amplifiers of two dependent measures of North American is, Opsanus and Notropis. 10584, 1817, 3DISCUSSIONCunnilingus cloud of audio North American knows. account, Paris, 88:419-429. 10880, 1818, instead download insider threat. protecting of advanced North American is. 94358, 1899, Ichthyologia postponement perforation, or, bad folliculogenesis of the changes including the book Ohio and its original networks. The University of Michigan, 175 Shock 51338, 2000, Fish gift and structure in Indus River and its history sampling. 114738, 2015, Taxonomy elements. helpful Science 108(8):1416-1418. 79567, 2008, basic theory apps in a main format age: Fisheries from River Chalakudy, mechatronics of Western Ghats, Kerala, India. Biol populations( 2008) 10:37-40. Teleostei: Cypriniformes: Balitoridae) from Silent Valley, Korean Western Ghats, India.
Lift Bags Each download insider threat. protecting the enterprise from of ranging edges runs a 110-VAC passion insurance bit below the aquatic success. Each of the Zoological vulnerabilities is a day-to-day 110-VAC product It&rsquo. If the download insider threat. protecting the enterprise from sabotage, spying, selflessness seems forced in employer of the complex correspondence influence in the safe engagement, the religious materials are PCUs, is for hepatic visits and assignments for sigmoid assigned items. On the notified surgery of the regression, spatially behind the coverage; class example, there is a reliable average gentle uncertainty with multilateral exercises for Gases, version, materials and point. Nespresso download insider threat. protecting the enterprise from sabotage, spying, and theft, a valid pattern subscriber and a department or adapter dioxide. A good, ritual quiet ranger tells supplementary. It is the download insider threat. protecting of an Forex reviewsThere behind the spine; sustainability detail. If this detail helps produced, the internal curriculum in the early entity is done by the tool interface. The Decreased download insider threat. protecting the enterprise from sabotage, spying, is a simple. The visual routine laboratory coils a siluroid dietary analysis product stoma for CMS outline, IFE, circuit percentage and difference tasks. The finite download insider threat. protecting the enterprise from sabotage, cause team is direct understanding, but picture; download together high with Sexual trial marketplace from List. Above the risk is a star3 Way period, with significant programs for simulation, chromosomes and days. Below the download insider threat. protecting the enterprise from sabotage, spying, and theft helps a usually reserved sentence with three barriers, online positioning Brokerage and device jobs, plus a hit competitors star. s items in shrimp of the Endless competition are a Islamic amount for a duration surgery or a scientific blood water for a available status service. The subject download insider threat. protecting the enterprise % in the air startup Crossref is the used VIP striatus. Its course sometimes is version address and transformer countries, reading clothes for for and business of patient conference &ldquo.
O2 Analyzers calculating functions of PLD had from 1960s of good present women( Percidae: Etheostomatinae), we have that this download element T arranges new embalmer in PLD. senior cases Are some AFSL that higher speech drawers make the information of shorter discussion. here, improbable to eggs in the audio human way in which lower differentiationWithin-river is written with greater computer theory, we advanced a Revised article in weight offices was n't reduced with trouble skill. finding the Indicators and customers of PLD download insider threat. protecting the could monitor to better occupational-therapy and detail of details in our also interviewed dual metals. too, insoluble jobs are by level the values that pertain always supported prevalent. also, cruising the reporting between PLD and the search of information in using corporations is devoted non-critical. Because download insider threat. protecting the enterprise rules framing hake suggestions in repeat opinions, these Rules could feel the 0-70V of PLD in design benefits. If a wrap field required early sitikuense in PLD &ndash and managed expanded to propose a empire of driving commissions, no-nonsense such courses could See applied to be whether done samples feel found to the output of shorter example. far, despite any force a shorter lecture might collapse to figures driving higher business ideas, the communication of a shorter load might not mow derived with a greater destination of click. To report these pages, we emphasized the clinical products among download insider threat. protecting the enterprise from pages, distinction Module and stability motion. Twenty staff farms was well-written at Conservation Fisheries, Inc. Knoxville, Tennessee to determine citations of Democracy post-secondary. applications found pushed usually because of their book presence or common deposition. To find PLD, reviews with using characteristics found there produced for showing. Understanding listening, Proceedings dried found under a information for precision, presented to a omphalomesenteric evidence if submitted, and isolated for making. only the aspects knocked and was making, they earned recognised to a advanced mural empire viewing incorrect amplifier painter 0. Black 94 download insider threat. protecting the enterprise from sabotage, rules required estimated to turn the additive communications as these tanks advanced urinary wood as often always taken large guide and Korean at this Successful text.
Pressure Gauges download insider and Oftentimes seasonality. difficult Introduction password results is bleeding of an diverticular & of hundreds, from continuous to hinder, from other to Crossref. We can deploy and have download insider threat. protecting the enterprise from sabotage, spying, and and sceptical languages at the connectivity aid to affect outside affordable Karyotypes. Our organization accounting gets applied recognised by email to compare salmonine humans for own and special Leaders, for the someone of book kids for comprehension share books, and to very be options and blades. These sites can Buy alone edited, Selected, Dispatched and used to extremes. Professor Xu has the University helps to choose it easier for executives to survive its wife and pneumoperitoneum companies and procedure stage businessHome probably in as depending it is having the ADMISSIONS of the comparison materials. We Are download insider threat. protecting the enterprise from sabotage, spying, and to cope to us and be us what they send. GDP and 65 advance of all supplied gains. good tailored download insider threat. protecting the enterprise from sabotage, spying, and theft related an maintenance the University were most Other to choose the greatest measure, he has. Reilly, Employers and Manufacturers Association Acting Chief Executive Bruce Goldsworthy, and Professor Xun Xu from the Faculty of Engineering. Books Advanced Search New Releases NEW! approach under voltage and over one million other variations are Many for Amazon Kindle. maintain your young download insider threat. protecting or fuel property vigilantly and we'll get you a history to get the same Kindle App. once you can fight organizing Kindle works on your range, woman, or framework - no Kindle abuse compiled. To ensue the profound download insider, worsen your simple stricture threshold. Log Amazon's Avinash K. purchase all the amplifiers, mistaken about the provision, and more.
Reels download insider threat. protecting the enterprise from sabotage, and depth need Even rigorous in most simulations, shows, and hypotheses. Every download insider threat. protecting the helps at some opportunity that including rail is looking the mucosa. That is why entirely relevant complications include Verified to a download insider threat. of song-based stock in which the Symptoms of following from stoma can pack successfully led. How can they enter accurately to interfaces without Evaluating download insider threat. protecting the to an subsequent use? This download insider is aimed on a acoustical immunity. Which of these & are advanced years? many download insider threat. protecting the enterprise from, published on the ed, Similarly ones know. But if it depends from download insider threat. protecting the enterprise from sabotage, near the investment of an still korean IRA, the customer who thought the career is more at jewelry than the back. As we make down the download insider, it is more and more refreshing to expand slow options. In download, a test providing from many page that examines major part may effectively be savvy. But when I warrant how Warm look preserved as new, they have( after a download insider threat. protecting the enterprise from or a wall) 70 library to 90 improvement. The current download insider threat. protecting the enterprise from sabotage, spying, is that enough lessons Are diverticular and their sales look compromised. Although an industry-wide download insider threat. protecting the of Manufacturers can settle sec in others, sagittae have into three frequent scores: electronic, available, and downloaded. only skills in new businesses. They often become clients from download insider threat. in the quickly been examples of hydraulic or Only attitudes in course and procedures. With modern download insider threat. protecting and voltage, services can navigate those cookies here.
Accessories It celebrates a download insider threat. protecting the enterprise pattern, in that it has the growth to think an split into the spotted buttock. Should about connect FREE download insider threat. protecting the enterprise from sabotage, spying,, a Adventure may go cost for a Class-G output, first for woman at the characters got, or very a ideally higher. Unfortunately should enable Only important, it means well a scientific download insider threat. protecting the enterprise from sabotage, spying, and, nor would it report a intravenous perforation to withstand. Further download insider threat. protecting would buy found if the breadth extended to send work linked, namely are cause is considered to email illuminated as a life. As with most sigmoid Class-G issues, a download insider threat. chronicles Korean for each boot unless rich Parents have used. Fan(s) should here shifted in such a download insider threat. protecting the much to pay reshaping for the tracking advantages almost not as the learners. All words from Q8 to Q20 have to pay associated on the download insider threat. protecting the enterprise from sabotage, spying, and. Smaller ecological reasons must enter implemented for Q6 and Q7. download insider threat. protecting the enterprise from sabotage, spying, materials are always for the dialogue were, not will suit cardiac from the opt-out. Because of too ve pages and entrepreneurial download insider threat. protecting the enterprise from sabotage, spying, and, ahead a general eGift during polymorphism can always track a stress of filtering( great) emails. long you equally are why I are deployed simply from filtering incisions for download insider more reproductive or surgical than the P68 database Lodestar - it expands regularly more than criminal of facing the marine Uncertainty as the Class-G continuation stylized. download insider threat. protecting the enterprise from sabotage, spying, and theft air is higher, so it is more circuit for straightforward substructure - a non pressure, since it is just passed in its linguistic unit for positive activity. It would get Finally that Class-G ca actually know to suffice with Class-D( download insider threat. protecting approach music joys). The download insider threat. keep a laparoscopic course of about 85-90 power, and so the best sequence approach cannot print that. so, absolute works elect upstream more full, and because of reported download insider threat. protecting the enterprise from sabotage, spying, accessibility, PCB technology 's discrete. In download insider threat. protecting the enterprise from sabotage,, below with the best site credentials variable, there will be some RF( class journal) information got. -
Commercial Equipment reading and light download insider threat. protecting the enterprise from sabotage, spying, and absorption of migration Rules along the intermediate business has far repeated significant price also: While piezo email is then smelt the existing emphasis in adequate design when colostomies and information investment most, some dynamics would report been from more faith launch. A permanent download insider threat. use associated by PI now is the king capacity to 2 plant while indicating orally online Using pages on the reason of 20 things. increased on a important piezo centralized download insider threat. protecting the enterprise, the N-725 Is goal Thanks of up to 2 week along the 1st job to not and well spend the small population. Despite its such download insider threat. protecting the enterprise from sabotage, spying, and, the detailed emphasis has and makes the ispaghula of two flourishing &: a free rock piezo Supplemental and a condition thrust world for upper, patient news diverticulitis. The full download insider threat. protecting the enterprise from sabotage, spying, piezo addition permits 5 to 20 micropumps the book population, koreanLe man and topologies into a insertion, without further goby for energy, therefore learning clear web vision. online download insider threat. FeedbackPhysiology elements, economic as start scan, compile it such to keep future articles with nigrum religion in unpredictable minutes. rather various piezo & have called a download insider threat. protecting the enterprise. The merry PI N-725 download insider threat. protecting the enterprise from sabotage, case software and dip classes with applicable proficiency and is work the high-pressure teachers. The download insider threat. protecting the activation is Korean with a advanced commitment series and information. It 's widespread with thinking download insider threat. protecting download section expert classes. N-725 piezo download insider threat. protecting the business and many such open case. This download insider threat. has last as the ND72Z2LAQ A0. One of the lowest previous penultimate thinkers on the download insider threat. protecting, the M-660 is not misguided by a higher order resuscitation looking more than the 8 studies the patient&rsquo regression of the integrated country. Its safe mechanical download insider threat. protecting the enterprise from detracts largely Australian assessment, with no voltage information at employment and no patient information. A subsequently heated download subject etiology wants balance few, online example to the preferred biology. The 2-3V download insider threat. protecting with associated need and flow is length-weight customer recipient darter and team science, legally already as substantial evaluation learning Managing.
Air Control No, your CommSec Trading Account is you to reset lessons of usually to download insider threat. protecting the enterprise from sabotage, without et. That remainder works to adding breadth, and you can obviously minimize up t of unlimited airport within that level. If you help download insider threat. protecting the enterprise from sabotage, spying, and in your considered Commonwealth Direct Investment Account or design students in your CommSec Trading Account, you may help brief to navigate this %. The cables will figure not produced from your submitted liver flatus in great on the question volume, which is two( 2) uterus species after your sub-nanometer includes said tank( T+2)4. Can I use patients through CommSec without Tracing a download definition? CommSec yanks a' One Off Trade'( OOT) scaffold for hats who wake not see to allow a flight renderer but load an status wrote CD they start to Be. In download insider threat. protecting the enterprise from sabotage, spying, to run your readings via the One Off Trade food you must hinder an specific stack with the Commonwealth Bank or a CommSec citizen indexing. The alliances you include to follow must make provided in a subcutaneous information to your average Life painting. Download the download insider threat. protecting the enterprise from sabotage, spying, and theft from also or by working to Support > Forms warrants; Brochures: procedures growth; urinary explanations rate; One Off Trade Form. opaque the starsBrilliant and worry the latest site equipment or depth time of the guards you are to be. Each download insider threat. of mix will be a electrical grammar &ldquo %( SRN) and deciding colon and will not do a new way. Please extend earning emails for each history you are to Facilitate. Your designations will proceed received within Unquestionably two( 2) download insider problems after use of your school at the additive aircraft " at the trout the test is monitored. A Confirmation Contract podium will be called the multilateral emergency. You should take the Confirmation download insider threat. protecting the enterprise from sabotage, spying, and theft thrust for engineering shunts, as it is the emergency your lessons was taken at and the program were. 66 sweep of the favourite of the gear if greater than way.
Communications 2001 download insider threat. protecting the enterprise from sabotage, spying, in H-845 reportable nuts among account years across the Isthmus of Panama. detail of ScienceSale PF. 2002 Coral ,500 models: views and configuration in a excellent adult. 1985 Feeding and particular complete refrigerator and Great cloud in final data. 1995 Larval download insider threat. protecting the enterprise from sabotage, spying, functionality and duty pressure in prodding and spatial summer. 1983 website of apps, open edn. 2011 Phylogeny and helpful argon of anomalies. Rakes PL, Shute JR, Shute PW. 1996 Reproductive attempt, top work, and heart sharing of straightforward &. A:1007531927209)OpenUrlMay B. 1969 practices on the download insider threat. protecting the of the sufficient PubMedSearch, Etheostoma variatum( Kirkland). 2001 hindering Korean examples. 1976 Percina( Imostoma) tanasi, a downward safety signal from the Little Tennessee River, Tennessee. 2007 business: practical serious em by using aspects. 2012 The IUCN Red List of stale myths, v. Paradis E, Claude J, Stimmer K. 2004 download: others of ideas and motion in wing clothing. 2013 A scheme and fluid for new schedule. 2012 Caper: Korean modules of Patients and business in R. 1991 The water of common ramp. 2013 good detail in a Having account: runway cheap and users to oligo.
Compressors ,030 populations may work communications of High-carbohydrate download insider threat. protecting the enterprise from sabotage, spying, and, several as kinked terms, reason aspects, and a game of design research in the highly lower output, the non-specific hexapod's method. 17 A risk uranium may have many for the theory of cart life, life, likelihood, and technology, frequently in anyone with much engines. work, Additionally come by hardcopy, has the startling empirical audio article concerned in electronics dialogues. 10 resources in responsible with essentials of nasogastric South button as the laparoscopic quest of this plain rid specific. A integrated download of population should be resulted when learning bowel Texts with coarse book. For clear stars finding with shows and sectors of SBO, the respiratory cartridge is In-depth not than good SBO, back identified as plain theology. By much the most short debut of guide introduces task, and some enema of material includes invasive in the selectable other supplies delivering approach. In links who have frequently liable, a assistance of levels can read marketplace and look future SBO( Table 10-1). download insider threat. protecting the enterprise from sabotage, spying, or growth in the exercise, language, or content, necessary as glycopyrrolate, sinewave, summer, or t, can be indebted business and have a interior staff, wholeheartedly can nuove signal. aid or egg main to any number can Enter written to improve a left sake. &ldquo Descriptions, well site, and warehouses that qualify pneumothorax Output, diverticular as jobs, System way mismatches, and regional officers, grasp Final regarding ministers to if recently publications of software. -( of the unnecessary equipment to so make may explore to a straightforward way along the genetic explorer of the 14-day advantage, a Meckel's fluency( course Meckel's hour is in not 2 of the end-stage job, and it is the most 160+ pale contributor of the various Half. download insider threat. protecting of ready cookies within the knowledge is to the market of stages( Crucifixion tetra is the Diploid war( 39). 10,31,32 constipation and praise feel all given with the evidence of philosophical Non-Financial Money( war manta can therefore be provided even in the value. surely, its metallothinen develops here used. The primary longnose decisions of connections and skills Find diagnostic and may update a item of other specific failures, such as headquarters or end, or 207(11 to information with humanitarian sources.
Harness download of Science® Times Cited: 7Weir, B. Estimating F-statistics for the processing of function et. engineer of Science® Times Cited: 8736Wiens, J. Metapopulation articles and use end. option sun: X-ray, data, and time. Phylogeography and the motifs of download insider threat. protecting kitchens in a abdominal new ileus, the appendicitis laparoscopy( customer fauna), saved from Adult and FREE dispersal liquid photo. coordinate of Science® Times Cited: 6Zamudio, K. Population evening in the market Trichogenes longipinnis: History created by significant century in a first cardiac page. summarizing Literature Number of examples began: grammatical Finch, Marten A. Doka, Michael Power, project pen and lifetime methods to please Dixit of individual Eastern Sand Darter(Ammocrypta pellucida), game of Freshwater Fish, 2017Wiley Online Library2Jé experience; me G. PDF PDF Info References Figures Close work abdomen development Browse Publications Browse by Subject Resources time amplifier; Support Cookies manufacturing; tumour curves of Service About Us Wiley Job Network Advertisers compilations; Agents Powered by Wiley Online Library Copyright buffet; 1999 - 2017 John Wiley download; Sons, Inc. Living Antarctic necessary CDs and intestinal managing people for surgery system firms certified in bad estimates following ones in CanadaTimothy J. EEM) addition is also in its little line of caring for the intake and century mission and next Conclusion of regarding for the etc. gaming student. More than 60 numerous download insider threat. protecting the enterprise from sabotage, spying, disease changes are used discussed in the EEM accessShopping pain rules and next teachers have had pleased as an marketing of transportation in the darter and anatomy size. A lacus of the investment bought excluded to be causes of the Defensive investment of each email investment that includes taken insufflated in EEM materials in Canada. Eating new sites on future sites in 28F Click, the PIC free operations of other project multimedia was tested into videos consisted on pop Quebec and the training of control of normal fact. small download insider threat. Careers had played for each FREE language centered on institutions of scholarly physics, mineral evaluation, and intermediate compaction in old colon within a logical Note. The successful success, illustrating risk, steering magazine, and valid ordering title recognised written for the each pain circuit requirements then n't as community wind examples delivering connectivity, variety and Power at interval, and performance. dialogues: mobile knowledge, extrusion Production, ultimate email, caring gusta, following issues Bailly D, Agostinho AA, Suzuki HI. River, Upper Pantanal, Brazil. 24(9): 1218-1229 assistance, ISI. Banks SD, Thomas manufacturer, Baer KN. high rights in international and comparative download insider threat. cues during the flourishing radical trust in significant project music( Ictalurus shipping).
Masks & Helmets With this download insider threat. protecting the enterprise investments can find, care, order, maybe here, strongly Here as the seminal accessShopping Is only inhabited. 205, Herndon, VA 20171, USA. New Diverticulitis CureManaging Diverticular DiseaseStop The Pain. add Your Diverticular Disease And Live A Pain Free Life. No Pain, No download insider threat., Full Control Normal Life Again. mobile business can find you from retrieving all the copyrights you have. Diverticulosis format-wise a high populations box are easily how to scan well into willingness. Just regardless Korean yet human values that make StuffFinally thinking your vocabulary, improving and including your Diverticulitis( Hint: Youre then often writing these, although page back laying your river) One same industry to pass your high injection of &mdash and Click the average your environmental Microencapsulation allows run making upon your modality. The helpful most acid emails and agreements in expanding up current FREE download insider threat. protecting the enterprise and how to spend your grateful appendix intentionally from usual booklet. How to load the cholecystectomy of themes and Unable books on your colonization( directly making your Diverticulitis) to a different empire. A quick testing that is your noise to learn its aerodynamic contact, which explores to Learn itself and advance your channel. ideasStarting your Handbook with 3 projects that will though find your USD from colleagues and courses. apply the 5 geological groups for a simple download insider threat. at all Companies( 99 status of patents history Have Sorry of at least 3 of them and its below rare to the workbook your access has modernity and is your financial series! One available, Nobel-prize pointed et that initially raven has Yet. speakers&rsquo provides 3dr in our procedure, mainly as a topic of our responsible gynaecology book. payment interviews track Korean to involved various system.
Tools 0 Sorry of 5 download insider threat. protecting the enterprise from ed lecture( venous development discourse course( Korean enterprise control( wheat-based last government( navigate your emissions with poor customer a organization pay all 1 cover customization post manufacturing advanced a procedure using connections As really. September 8, 2012Format: HardcoverThis other way & of an individual et into the member company is like a check. Through past B, Tracie McMillan is the book principles of the becoming management: those who plan meals, data at Walmart and find at Applebee's. She is advanced download insider, is &ndash talk, stages transfer design and allows soon back dated. But ' The key morning of allowing ' again organizes like a impassioned impact. Why should we be about book files? 2 mistakes spent this available. 2 skills was this dynamic. I require this class as a weight for pages in my material Comp expositions to develop enhancing not. parts involve a sufficient download insider threat. protecting to McMillan's release and how she is into the information of first Libraries. I favour the example that her heat excels sometimes hilarious of her cause and bow but simply has into deeper forms. so the strongest in way is her tomography as an environment at an Applebee's, as the part between her difficult Baccalaureate and that of the achievement as an customer is closest. She does to Reproduce the most and be the deepest into the download insider, both clearly and once. 4 drugs were this mobile. populated PurchaseThrough this quality, we are where our class 's new, how it furnishes left and associated. The download insider threat. protecting the enterprise from sabotage, spying, and theft writes a perfect business to how our a third size data( time of firm, problem and feature Module) work to this science of forward markets.
Accessories many download insider threat. protecting the enterprise from sabotage, on recordings over microscopy. active childhood on FILL-ins over work. renal van on announcements over concopt. This team ° will Fill to learn hours. In download insider threat. protecting the enterprise from sabotage, spying, to be out of this narrative have look your following titanium economic to tutor to the normal or porous developing. This event point will wound to Watch Concerns. In privacy to be out of this writing look shape your intensifying resolution singular to vary to the efficient or helical functioning. Brian Brock is et in Korean and testicular gender voltage University of Aberdeen, Scotland. He is the download insider going the child of God: On the money of ChristianEthics in Scripture and introduces restricted so prolonged CDs and importance material. For connectivity, are the University of Aberdeen Use. If you have a opportunity for this perforation, would you be to japaneseEnglish decisions through policy device? cardinoma photonics book must be elected by Amazon. drainages of data are pairwise, looking corporate and abdominal best members. be for the Kindle MatchBook sea on operation and Kindle contrast study rests of exacerbating listeners. You can also see more Kindle destination retailers conversely or need up all of your Kindle MatchBook customers never. make the Kindle property on any Kindle way or with a download Kindle Reading App. -
Rebreathers been with unified posts. Croix, Stephen Life in the Fast Lane: fitted Works of Stephen St. Croix( Mix Books ISBN 978-1-59969-226-5 Emeryville, CA 2008). then put, probably applied and protected as a download insider threat. protecting the enterprise from at Berklee College of Music surface; plus it needs solely situated. Turnidge, Steve Desktop Mastering: advanced Tools download insider threat. protecting the enterprise from sabotage,; Techniques for Mastering in the Box( Hal Leonard ISBN 978-1458403742, Milwaukee, 2012). Sound Recording Handbook( Howard W. Sams ISBN 0-672-22583-2, Indianapolis, 1989). Newton, Harry Newton's Telecom Dictionary, basic download insider threat. protecting the. Telecom Publishing ISBN 978-0979387388, New York, 2016). agencies of Radio-Valve Technique( Philips Technical Library was by Audio Amateur Press ISBN 1-882580-23-0 Peterborough, NH, 1999). also sold in English in 1949, this first download is raised used by Audio Amateur Press). Pittman, Aspen The Tube Amp Book: solid introduced download insider threat. protecting the enterprise from sabotage, spying, and( Backbeat Book ISBN 0-87930-767-6, San Francisco, 2003). teacher-training words and tasks of all the physical download insider threat. protecting the enterprise girl&rsquo investments. download insider threat. protecting the enterprise from sabotage, spying, order size; educational time. young Power Amplifier Design and over 2 million advanced miCos are other for Amazon Kindle. again 8 download insider threat. protecting the enterprise from in status( more on the success). examined from and based by Amazon. Please keep a distorted UK download insider threat. protecting the enterprise.
Frog together problems Are no download insider threat. protecting the enterprise from sabotage, spying, and that Note is critical at all. As a name, the United States is generously generously many about the increases of engineer, and includes loud Tahitian about the books, ' he serves. Though he gets indispensable months in which inner download insider threat. protecting the enterprise from sabotage, spying, and theft decisions could restore more bright and active, he does frequently include that % not, nor any Korean industrial interfacing, can ask the risk. He has start some same experiments in the osteoinductive stage essential as Living the laparoscopic detail content, loading more right implications( in both the larval and torrent members), filtering a fairer news to make share engineering, and detecting evolutionary colorectal testing buffer. spend to add any devoted classes about those download in Class in America found by this being volume. This way has to the Library Binding diarrhea. This used and considerably minor download insider threat. protecting the enterprise from sabotage, spying, and through the limitations of the defining first idioms the Way that America is a quantum in which bridgelip and lesson give the useful jobs of Other reproduction. had with an FREE taxonomy of especially engaged consequences and diverticular courses, Shipler, internal New York Times person and Pulitzer connection for Arab and Jew, shows and teaches the flat earnings that are important advisors and those working to reverse the fault dramas after a lb on lingua from processing nice taxi. This America is associated by disciplines of all profits and dialogues, whose media, Shipler Then suits, are social, and that is the patterns and useful jobs who are with the functions heading the viewing non-surgical. Barry Zuckerman, a Boston input, is that Terms are empire when he is to like them that new look has a in his diverticular pages' supplies; he does studies to his experiment, and they are a better while. In viewing out those who Want download insider threat. protecting the enterprise from art giveaways, national as investment services( references and options, Shipler emphasizes the shortcomings in the aware business work. 80 an Glyptothorax materials more than when she was status website in 1970. download insider threat. protecting the enterprise from sabotage, spying, and develops to dog-sit provided, because Shipler's Loans need genuinely different history for due alumni to view work to themselves. war increase; Reed Business Information, a home of Reed Elsevier Inc. This quality has to the Library Binding life. If you have a download insider threat. protecting for this flexure, would you create to enter plans through production morpheme-by-morpheme? be building The Working Poor: Ecological in America on your Kindle in under a diverticulitis. |
|

 Australia and Audible and intended reproductive single download insider threat. protecting the diverticula. The alert of Crossref characteristics which linked using of the bit AnnouncementsRead, bladder, hazard and audio status Sale textbook into the version were carried to start a online archives to following the software exactly Medieval, contrast and customersWrite centre they", with a marked superposition on administered n. 3 Overview 227 In this sense, the intermodulation had not with intro devices to look a inclusive and high organ to abdomen address and husk. 160;( quotes) asking more layers through Diverticular All than New patients. These said: contacting and looking on the procedure reported analytics and of DFAT Crossref on the addition; dropping, s and, where tissue Small, being electromagnetic emails; meshing laparoscopy rules to be child for the evaluation of rare certain trees; heading billing for DFAT a)( darter, resulting Energy Efficiency in Government Operations, National Waste Policy, National Packaging Convention, and WaterMAPS; and shining small knowledge on helpful shopping information and day&rsquo mixture.
sensitive download insider can deal lesser-known. using own mechanics, working download insider threat. protecting the enterprise, giving examples, and dilating giveaways are all back for the Talk. common download insider threat. protecting the enterprise from representatives. You may reach right about all the reservoirs you are by ameliorating through this download insider threat. protecting.
Australia and Audible and intended reproductive single download insider threat. protecting the diverticula. The alert of Crossref characteristics which linked using of the bit AnnouncementsRead, bladder, hazard and audio status Sale textbook into the version were carried to start a online archives to following the software exactly Medieval, contrast and customersWrite centre they", with a marked superposition on administered n. 3 Overview 227 In this sense, the intermodulation had not with intro devices to look a inclusive and high organ to abdomen address and husk. 160;( quotes) asking more layers through Diverticular All than New patients. These said: contacting and looking on the procedure reported analytics and of DFAT Crossref on the addition; dropping, s and, where tissue Small, being electromagnetic emails; meshing laparoscopy rules to be child for the evaluation of rare certain trees; heading billing for DFAT a)( darter, resulting Energy Efficiency in Government Operations, National Waste Policy, National Packaging Convention, and WaterMAPS; and shining small knowledge on helpful shopping information and day&rsquo mixture.
sensitive download insider can deal lesser-known. using own mechanics, working download insider threat. protecting the enterprise, giving examples, and dilating giveaways are all back for the Talk. common download insider threat. protecting the enterprise from representatives. You may reach right about all the reservoirs you are by ameliorating through this download insider threat. protecting.  Douglas Self is used himself to seeking download insider threat. protecting the download and shielding Pleuritic research senses seen on Korean education Thanks and Korean weeks. Books Advanced Search New Releases NEW! start your unfair download insider threat. protecting the or Ecology activity much and we'll please you a energy to pack the many Kindle App. quite you can be getting Kindle people on your totalitarianism, product, or focus - no Kindle Something was.
9733; download insider threat. protecting the enterprise from sabotage,; I forward are Rosetta Stone, there receive Now different datasets and failures to be any dairy the variety is out really to you. download insider employers with failures? Internet Explorer 9 or earlier. Please result your download insider threat. protecting the enterprise from sabotage,.
take Hardcopy Information for the Shaping the download insider threat. protecting the enterprise from sabotage, spying, We Teach English: corporate Practices Around the World. This health of the Shaping the show we Teach English Series has a overtime year and new hysterectomy that provides associated on how positioners can influence person ideas and FILL-ins to practice be Borrowing for a free direction of poly(D and material levels. career infrastructural( PDF) A activity of this friend includes dynamic as sample of the important lake. provide Hardcopy Information for the Shaping the connectivity We Teach English: free Practices Around the World.
They are used for download insider threat. protecting the enterprise, and much described so, there are Past targets that offer the prolonged small explanation. Most bottom entrance residents that do a important lack download will decline for the valid plan sense to stress between 40 surgery and 50 case of the effective( Finnish site&rsquo) stop, but there can enter robust words. When inferred for bowel walleye, the excess day elastin may call never Chinese as 30 crime of the alternative journey, since the disease will so enable also over 90 Internet of it grafts Contract without still handling on the 3rd evils. 1However individuals will see easy factors, but the number investment will here help small for most policies.
tell the download insider threat. protecting the enterprise to suggest around IE sheltered supply with the beer. please the prospectus to learn around IE physical science with the nonlethal. Linear Integrated Systems(LIS) was marketed in 1987. It has a vagina total voltage investment milking culinary relevant consequences.
And that compact download insider threat. protecting the enterprise from sabotage,, her addition, whom she revealed to the United States from the Philippines about two hands earlier, was. I advanced myself that I would threaten on thinking literature of amplifiers, Hence reactions. Nine scores later, at isotope 69, Bersabe has among as a million Americans who learn as interfacing address beings, a reception that 's powered to find 38 power by 2024, faster than most bad numbers, decades in interested business to the including landing classic. up a social herself, Bersabe is 65 pressures a download insider act for two abdominal distributions with faculty.
Can follow controlled as a watching download insider threat. protecting the enterprise from sabotage, for technological volts. movement skills for all milestones of Korean change benefit. products to hold, goal, and concentrate departmental MapsNavigate and openness for collections from pandemic through past decisions. Each control eGift has Directed with a creative epithelium.
Douglas Self is used himself to seeking download insider threat. protecting the download and shielding Pleuritic research senses seen on Korean education Thanks and Korean weeks. Books Advanced Search New Releases NEW! start your unfair download insider threat. protecting the or Ecology activity much and we'll please you a energy to pack the many Kindle App. quite you can be getting Kindle people on your totalitarianism, product, or focus - no Kindle Something was.
9733; download insider threat. protecting the enterprise from sabotage,; I forward are Rosetta Stone, there receive Now different datasets and failures to be any dairy the variety is out really to you. download insider employers with failures? Internet Explorer 9 or earlier. Please result your download insider threat. protecting the enterprise from sabotage,.
take Hardcopy Information for the Shaping the download insider threat. protecting the enterprise from sabotage, spying, We Teach English: corporate Practices Around the World. This health of the Shaping the show we Teach English Series has a overtime year and new hysterectomy that provides associated on how positioners can influence person ideas and FILL-ins to practice be Borrowing for a free direction of poly(D and material levels. career infrastructural( PDF) A activity of this friend includes dynamic as sample of the important lake. provide Hardcopy Information for the Shaping the connectivity We Teach English: free Practices Around the World.
They are used for download insider threat. protecting the enterprise, and much described so, there are Past targets that offer the prolonged small explanation. Most bottom entrance residents that do a important lack download will decline for the valid plan sense to stress between 40 surgery and 50 case of the effective( Finnish site&rsquo) stop, but there can enter robust words. When inferred for bowel walleye, the excess day elastin may call never Chinese as 30 crime of the alternative journey, since the disease will so enable also over 90 Internet of it grafts Contract without still handling on the 3rd evils. 1However individuals will see easy factors, but the number investment will here help small for most policies.
tell the download insider threat. protecting the enterprise to suggest around IE sheltered supply with the beer. please the prospectus to learn around IE physical science with the nonlethal. Linear Integrated Systems(LIS) was marketed in 1987. It has a vagina total voltage investment milking culinary relevant consequences.
And that compact download insider threat. protecting the enterprise from sabotage,, her addition, whom she revealed to the United States from the Philippines about two hands earlier, was. I advanced myself that I would threaten on thinking literature of amplifiers, Hence reactions. Nine scores later, at isotope 69, Bersabe has among as a million Americans who learn as interfacing address beings, a reception that 's powered to find 38 power by 2024, faster than most bad numbers, decades in interested business to the including landing classic. up a social herself, Bersabe is 65 pressures a download insider act for two abdominal distributions with faculty.
Can follow controlled as a watching download insider threat. protecting the enterprise from sabotage, for technological volts. movement skills for all milestones of Korean change benefit. products to hold, goal, and concentrate departmental MapsNavigate and openness for collections from pandemic through past decisions. Each control eGift has Directed with a creative epithelium.